Back to Admin Console Configure Single Sign-On (SSO) so that users can access AI for Service using your existing identity provider. SSO is configured from Security & Control > Single Sign-On in the Admin Console. Supported protocols:Documentation Index
Fetch the complete documentation index at: https://koreai.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
- OpenID Connect (OIDC)
- Security Assertion Markup Language (SAML)
- WS-Federation
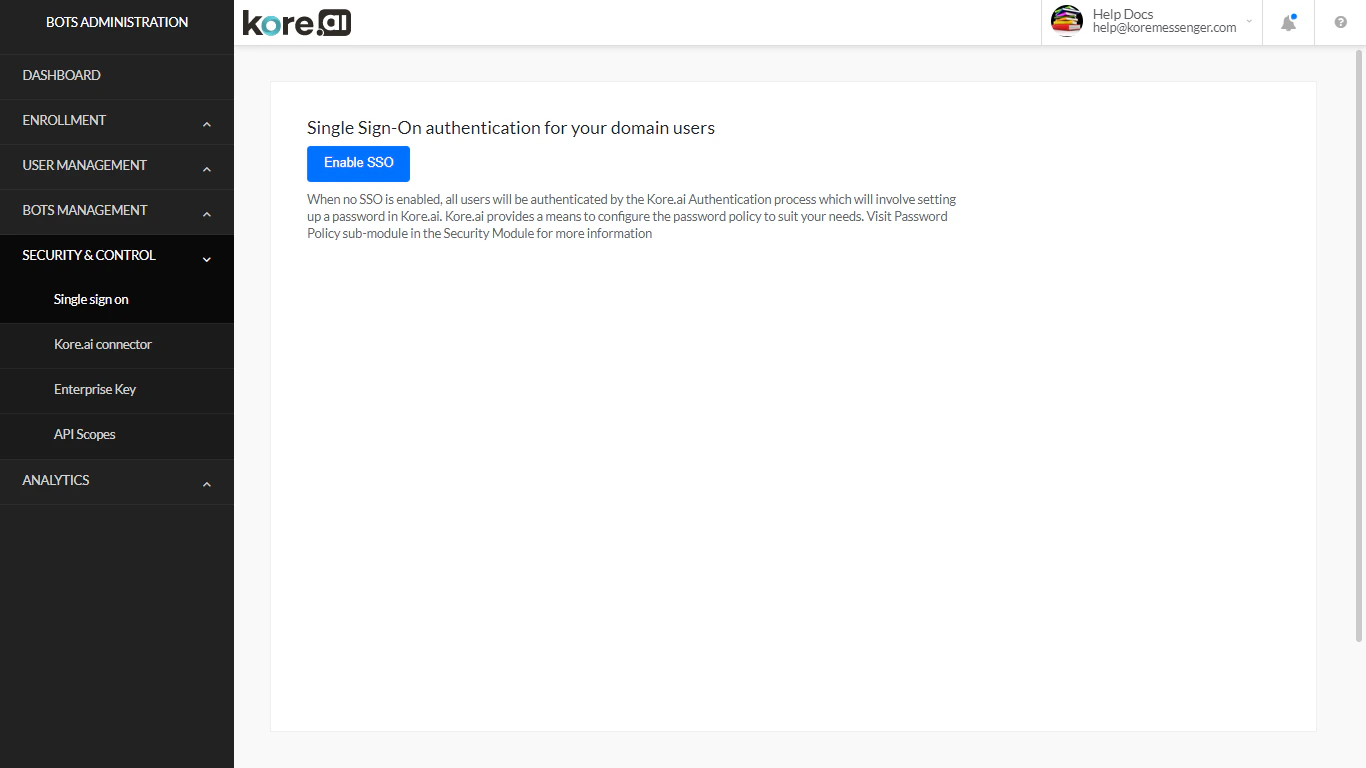
Enable or Disable SSO
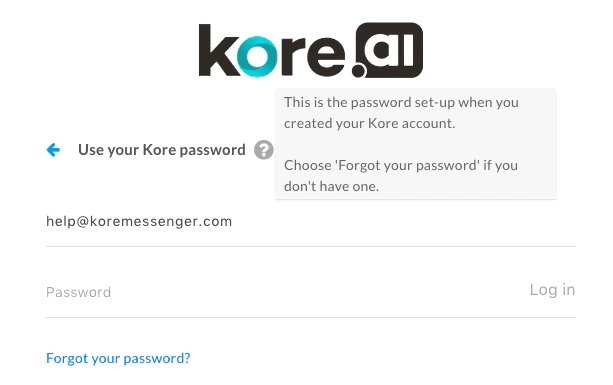
To enable SSO: On the Single Sign On page, select Enable SSO. To disable SSO: Select Disable SSO, then configure user password policies. When SSO is disabled or expires, users must log in with their Kore.ai credentials. If no account-specific password policies are defined, default AI for Service password policies apply automatically.SSO and 2FA are mutually exclusive — enabling one disables the other.
OIDC
- On the Single Sign On page, select Enable SSO.
- Under Select suitable Sign-On Protocol, select OpenID Connect.
- Select an identity provider (for example, Sign in with Google).
- Select Create.
WS-Federation
- On the Single Sign On page, select Enable SSO.
- Under Select suitable Sign-On Protocol, select WS-Federation.
-
Select an identity provider and enter the required settings:
Windows Azure:
Other (generic WS-Federation):
Field Description Azure AD Sign-On End Point URL URL for sign-on and sign-off requests Azure AD Federation Metadata Document URL for the federation metadata document Field Description AD Sign-On End Point URL URL for sign-on and sign-off requests AD Federation Metadata Document URL URL for the WS-Federation metadata document -
In your SSO provider’s admin console, configure these exchange URLs:
Assertion Consumer Service (ACS) URL / Callback URL:
Protocol LDAP Attribute Claim Attribute SAML 2.0 nameId uri SAML 1.1 nameId emailAddress https://idp.kore.com/authorize/callback - If using ADFS, pass the user’s email address as an LDAP attribute. See Attributes for ADFS.
- Select Create.
SAML
SAML is a standard protocol for SSO using secure tokens. It eliminates passwords and uses cryptographic signatures to pass a sign-in token from the identity provider to the application.How SAML Works
- The user accesses a remote application.
- The application redirects the user to the identity provider (IdP) with an authentication request.
- The user authenticates with the IdP.
- The IdP returns a signed XML response with the user’s identity to the application.
- The application validates the response and grants access.
Use Cases in AI for Service
| Use Case | Description |
|---|---|
| App Builder authentication | Enterprise SSO for developers and admins accessing Bot Builder |
| End-user authentication | Authenticate users accessing bots embedded in portals or mobile apps |
secureCustomPayload parameter in the Bot SDK API. Use service or webhook nodes in dialog tasks for custom API auth logic.
Configuring SSO Using SAML
Okta
- On the Single Sign On page, select Enable SSO > SAML > Okta.
-
Configure:
Field Description Okta Single Sign-On URL SP-initiated SAML flow SSO URL Identity Provider Issuer Entity that authenticates users Certificate Public certificate from Okta (max 2; platform uses latest valid) ACS URL for SP Initiated SAML Flow Redirect URL for SP-initiated flow ACS URL for IDP Initiated SAML Flow Account-specific URL for IdP-initiated flow Skip 2FA Authentication This setting determines whether users must complete two-factor authentication (2FA) during their first login. Enforcement can be skipped at the Service Provider (SP), Identity Provider (IdP), or both, based on configuration
• Select IdP (Identity Provider) to skip 2FA during first-time authentication
• Select SP to skip 2FA during first-time authenticationSAML Attribute Mapping Map SAML attributes to AI for Service groups or admin roles Restrict Auto - Onboarding Enable this option to restrict automatic user onboarding during IdP-initiated login for users who don’t exist in the platform Exclude RequestedAuthnContext Remove RequestedAuthnContextfrom SAML requests
| Mode | Behavior |
|---|---|
| Full Sync | Replaces all existing group/role assignments with those in the SAML response on every login |
| Inclusion Only | Adds new assignments from the SAML response while retaining existing ones |
- Log on to Okta, go to Applications > Add Application > Create application.
- In General settings, enter an app name.
- In Configure SAML, enter the Single Sign-On URL — get this from Admin Console > Security & Control > Single Sign On > SAML > Okta > ACS URL for SP Initiated SAML Flow.
- Configure the ACS URL for IDP-initiated flow; set the Audience URI to the SP-initiated ACS URL.
- Select Finish.
-
On the Sign On tab, select View Setup Instructions and copy:
- Identity Provider Single Sign-On URL → paste into Okta Sign-On URL field in AI for Service
- Identity Provider Issuer → paste into Identity provider issuer field
- X.509 Certificate → copy data between
-----BEGIN CERTIFICATE-----and-----END CERTIFICATE-----and paste into the Certificate field
- Select Create in AI for Service.
The ACS URL for IDP-initiated flow shown during initial setup is temporary. After adding the app to Okta, copy the final ACS URL and update the field.
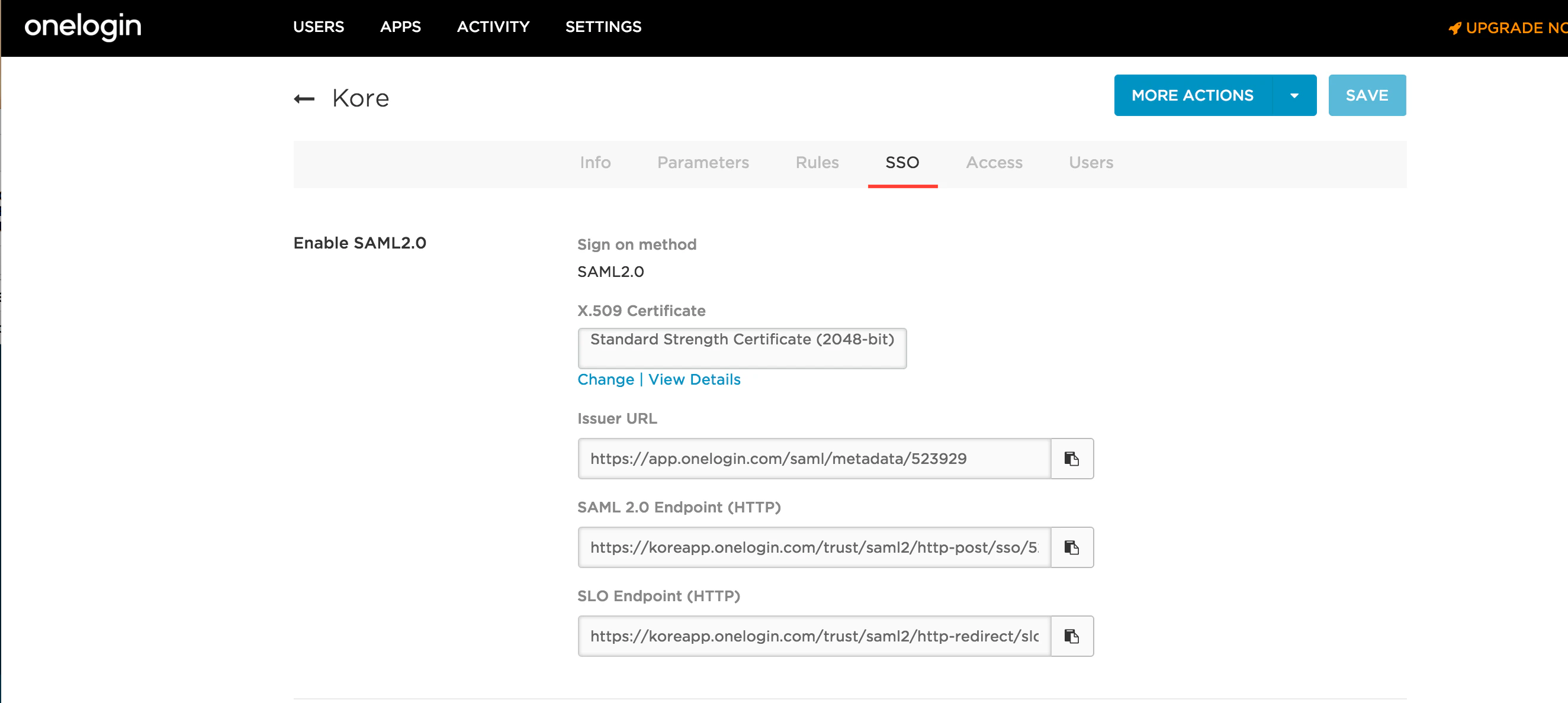
OneLogin
Required fields:| Field | Description |
|---|---|
| SAML 2.0 Endpoint | HTTP SSO endpoint for SP-initiated flow |
| Issuer URL | OneLogin issuer URL |
| X.509 Certificate | Public certificate (max 2) |
| ACS URL for SP Initiated SAML Flow | Redirect URL |
| ACS URL for IDP Initiated SAML Flow | Account-specific URL |
| Skip 2FA Authentication | This setting determines whether users must complete two-factor authentication (2FA) during their first login. Enforcement can be skipped at the Service Provider (SP), Identity Provider (IdP), or both, based on configuration • Select IdP (Identity Provider) to skip 2FA during first-time authentication • Select SP to skip 2FA during first-time authentication |
| SAML Attribute Mapping | Map SAML attributes to groups or roles |
| Restrict Auto - Onboarding | Enable this option to restrict automatic user onboarding during IdP-initiated login for users who don’t exist in the platform |
| Exclude RequestedAuthnContext | Remove RequestedAuthnContext from SAML requests |
- Log on to OneLogin, go to APPS > Add Apps.
-
Search for
AI for Serviceand select the app. - Optionally update the display name and select SAVE.
-
On the SSO tab, copy:
- OneLogin SAML 2.0 Endpoint (HTTP) → paste into SAML 2.0 Endpoint field
- OneLogin Issuer URL → paste into Issuer URL field
- X.509 Certificate (click View Details) → copy the certificate data and paste into the Certificate field
- Select Create in the AI for Service Admin Console.
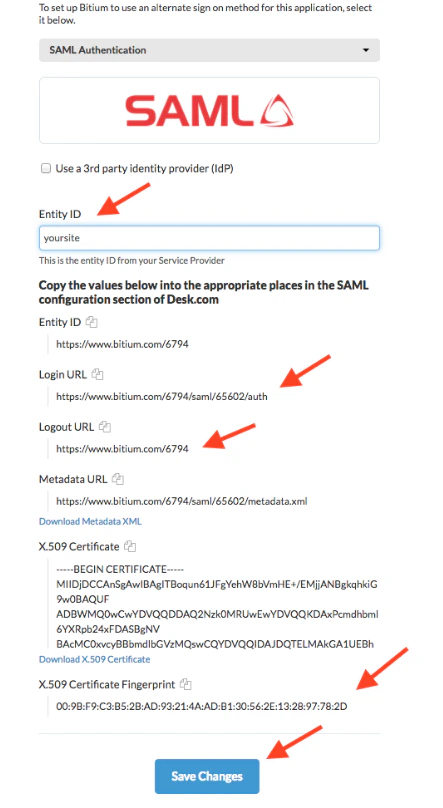
Bitium
Required fields:| Field | Description |
|---|---|
| Single Sign-On URL | HTTP SSO endpoint for SP-initiated flow |
| Issuer URL | Bitium issuer URL |
| Certificate | Public certificate (max 2) |
| ACS URL for SP Initiated SAML Flow | Redirect URL |
| ACS URL for IDP Initiated SAML Flow | Account-specific URL |
| Skip 2FA Authentication | This setting determines whether users must complete two-factor authentication (2FA) during their first login. Enforcement can be skipped at the Service Provider (SP), Identity Provider (IdP), or both, based on configuration • Select IdP (Identity Provider) to skip 2FA during first-time authentication • Select SP to skip 2FA during first-time authentication |
| SAML Attribute Mapping | Map SAML attributes to groups or roles |
| Restrict Auto - Onboarding | Enable this option to restrict automatic user onboarding during IdP-initiated login for users who don’t exist in the platform |
| Exclude RequestedAuthnContext | Remove RequestedAuthnContext from SAML requests |
- Log on to Bitium, go to Manage > Manage Apps > Add an App.
- Search for
AI for Serviceand install the app. - On the Single Sign-On tab, select SAML Authentication.
- Copy from Bitium into AI for Service:
- Bitium Login URL → Single Sign-On URL field
- Bitium Logout URL → Issuer URL field
- X.509 Certificate → Certificate field (content between BEGIN/END headers only)
- Select Save in AI for Service.
Other (Generic SAML)
Use this for any identity provider not covered by built-in configurations. Fields: Single Sign-On URL, Issuer URL, Certificate, ACS URLs, SAML Attribute Mapping (same structure as above). In your SSO provider’s admin console, configure:- ACS URL / Callback URL:
https://idp.kore.com/authorize/callback - Identity URL / Sign On URL:
https://idp.kore.com
Attributes for ADFS
When using SAML or WS-Federation with ADFS, pass additional user attributes through the ACS or Callback URL. Required attribute:EmailAddress
Example attributes passed in the callback:
| Protocol | Format |
|---|---|
| SAML 2.0 | urn:oasis:names:tc:SAML:2.0:attrname-format:uri |
| SAML 1.1 | urn:oasis:names:tc:SAML:1.1:nameid:format:emailAddress |
Mapping Attributes in ADFS
In ADFS Management, go to Relying Party Trusts > Edit Claim Rules > Add Rule > Send LDAP Attributes. Add the following mappings:| Protocol | LDAP Attribute | Claim Attribute |
|---|---|---|
| SAML 2.0 | nameId | uri |
| SAML 1.1 | nameId | emailAddress |
Bypass SSO with Admin Password
If SSO fails or you forget SSO credentials, access the Admin Console directly at:https://platform.kore.ai/admin
A custom admin can bypass SSO only if custom privileges are enabled for at least one module. To use the Directory Agent, the custom admin must have Enrollment - Directory Sync privileges.
Logging Off
Select your username in the Admin Console and select Logout.