Back to App Settings OAuth v2 is the new version of the open protocol to allow secure authorization in a standardized manner from web, mobile, and desktop applications. To use this authorization method, you must first register an account with the web application — you will need the log-in credentials for that application to configure the Authorization Mechanism settings.Documentation Index
Fetch the complete documentation index at: https://koreai.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
How oAuth v2 Password Grant Type Works
The oAuth v2 Password grant type allows apps to exchange a user’s credentials for an access token.- The Platform redirects the user to a login dialog at the web application.
- The user authenticates.
- The web application redirects the user back to the Platform with an access token.
- The Platform validates the access token.
- The access token allows the Platform to access a protected resource at the provider, on behalf of the user.
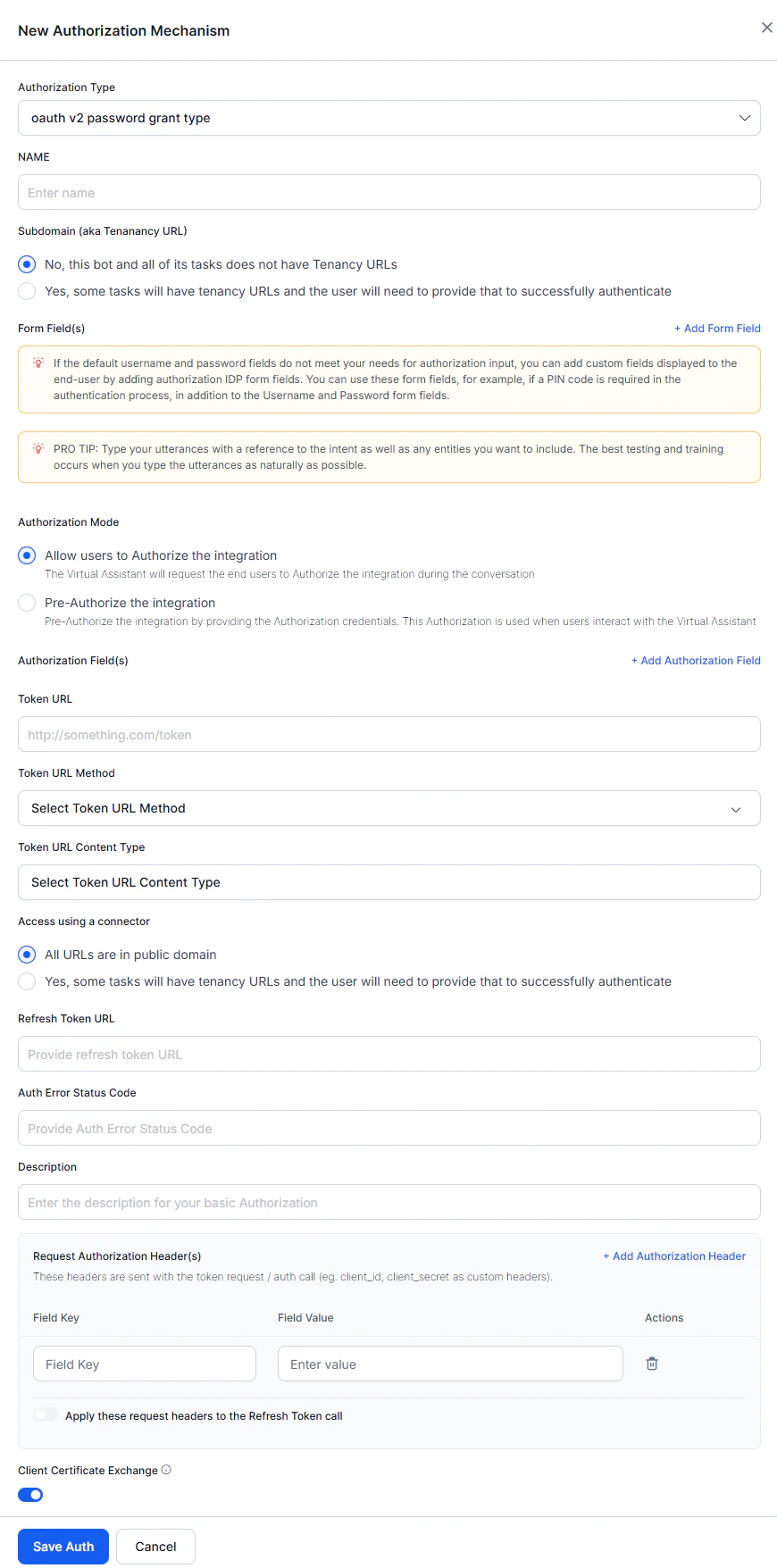
Configuring oAuth v2 Using Password Grant Type
- Open the assistant for which you want to configure an Authorization profile.
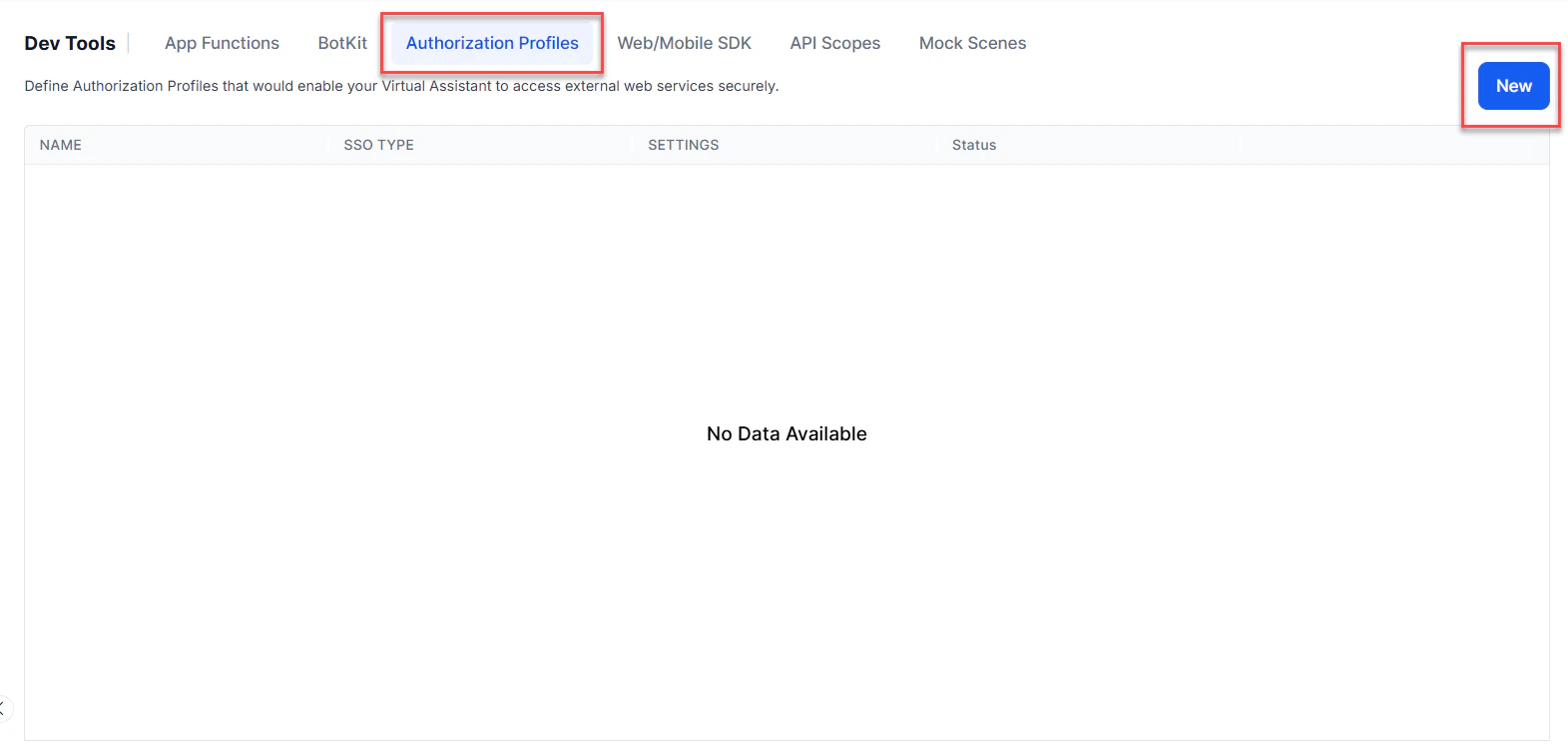
- From the left menu, click App Settings, then select Dev Tools > Authorization Profiles.
-
Click New to open the New Authorization Mechanism dialog.
- In the Authorization Type drop-down list, select oAuth v2 password grant type.
-
Enter a Name for your authorization, then define the fields to enable it.
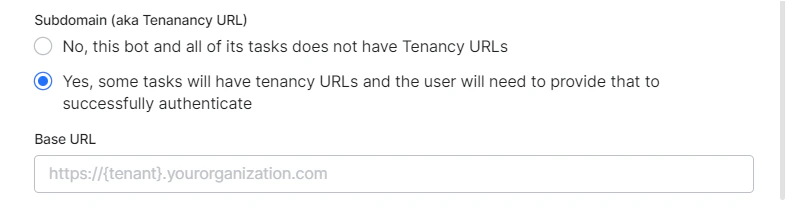
Defining Tenancy
If required, in the Subdomain section, select Yes if the base URL for a web application or user interface uses a tenant name in the URL. For example,platform is the tenant organization for a web service that uses subdomain-based tenants, such as www.platform.example.com.
In the following example configuration, the tenancy URL contains the {tenant} organization placeholder.
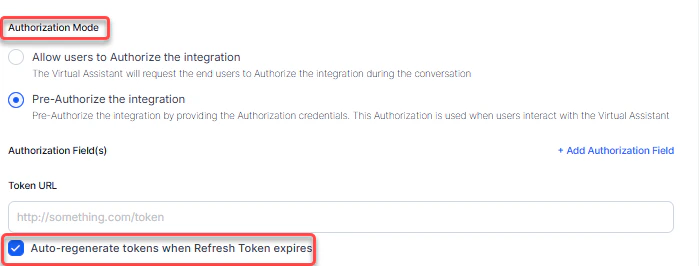
Selecting Authorization Mode
This section defines how authorization is handled for the integration.- Allow users to authorize the integration: End users are prompted to authorize the integration during the conversation with AI Agents.
- Pre-authorize the integration (Recommended): Authorization credentials are provided in advance. This authorization is reused whenever users interact with the AI Agent, eliminating the need for individual authorization.
Auto-regeneration of refresh tokens works only when the User ID and Password are provided in the OAuth v2 Password Grant Type. If these credentials are not configured, the platform cannot regenerate tokens automatically when the refresh token expires.
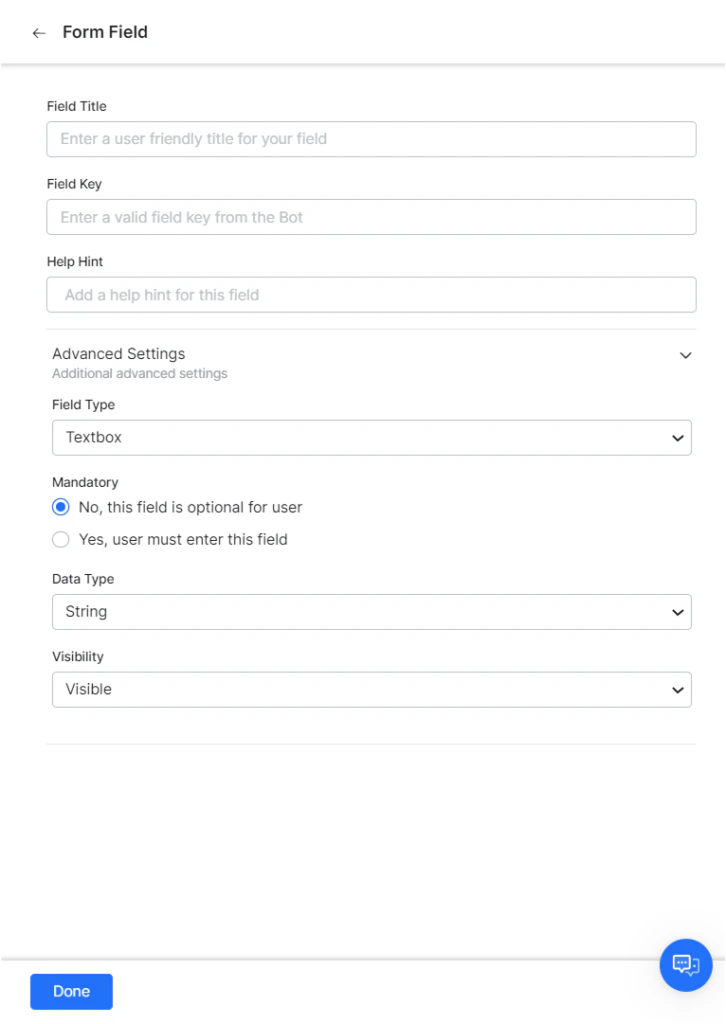
Adding Form Fields
If the default username and password fields do not meet your authorization input needs, add custom fields displayed to the end-user by adding authorization IDP form fields. For example, add a PIN code field in addition to the default fields. Click Add Form Fields, then configure the necessary parameters for each field. The following table describes the fields used to define an authorization form field.| FIELD NAME | DESCRIPTION |
|---|---|
| Title of Field | Specify the name of the field displayed to the end-user in the authorization dialog. |
| Field Key | The value represents the end-user input value to the authorizing service. |
| Help Hint | The help text displayed in the field to describe what should be entered. |
| Field Type | When Advanced Options is selected, specify the type of field displayed in the end-user interface to collect user input for the Field Key, one of: Textbox, Password |
| Mandatory | When Advanced Options is selected, select if the end-user must define this field to complete the authorization. |
| Data Type | When Advanced Options is selected, specify the type of data expected as input from the end-user, for example, String. |
| Visibility | When Advanced Options is selected, specify if the authorization field should be visible, hidden, or displayed as read-only. |
Adding Authorization Fields
By default, authorization fields are configured as part of the header of the request message. If your request requires additional authorization fields or the expected authorization is not part of the header (for example, social security number or PIN), click Add Authorization Fields and define the fields.
-
In the Field Type field, select one of the following depending on where in the request message the authorization fields are required:
- Header - The assistant expects the authorization fields as part of the header of the request.
- Payload - The assistant expects the authorization fields as part of the content of the body of the request.
- Query String - The assistant expects the authorization fields as a query in the body of the request.
- Path Param - The assistant expects the authorization fields as part of the URL path for the request.
- In the Field Key field, enter the name of the field for the selected Field Type.
- In the Field Value field, enter the value for the Field Key specified.
- Select Done. The new authorization field is added in the Authorization Fields section.
Defining the Token URLs
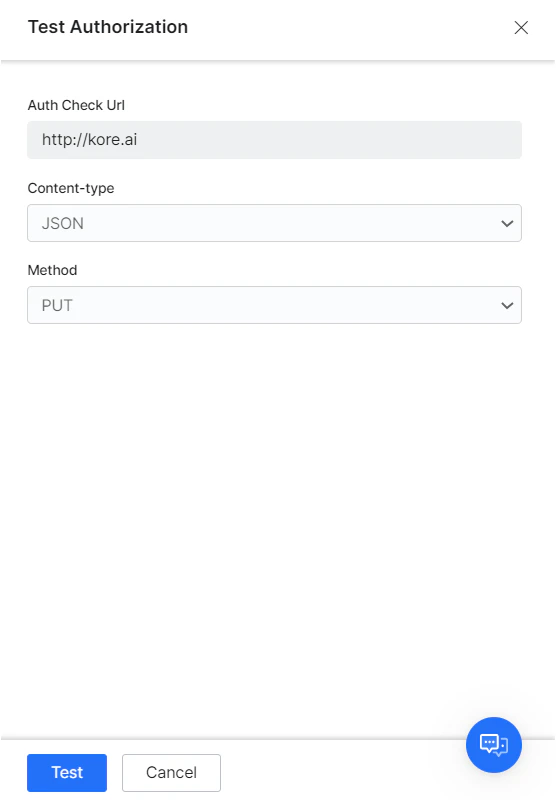
In the Token URL field, optionally define a URL to test the authorization settings from Platform before deploying the AI Agent. You can use dynamic fields, path parameter fields, query fields, and more. For example,http://{tenant}.example.com/test/{{tokenId}}.
In the Token URL Method field, select the HTTP request method type for the Token URL: one of PUT, POST, PATCH, DELETE, or GET.
In the Token URL Content Type field, select the content type expected from the Token URL: one of JSON, RSS, XML, URL Encoded JSON, CSV, Text, Twitter Encoded JSON, Multipart/Form-data, Multipart/Related, or Oracle ADF.
In the Refresh Token URL, enter the refresh token URL if required.
For authentication errors, enter the Auth Error Status Code.
Access using the Connector
In the Access Using a Connector section, select Yes to enable access for AI Agent using the Kore.ai Connector agent. If your domain has no active Kore.ai Connectors defined, a warning message is displayed to contact the Admin Console System Administrator. Click Save Auth to save the authorization settings and close the New Authorization Mechanism dialog.Adding Request Authorization Header(s)
If your request requires additional authorization headers supported by the external system, click + Add Authorization Header to configure the required header fields.- In the Field Key field, enter the header name.
- In the Field Value field, enter the corresponding header value.
- Select + Add Authorization Header to add multiple headers as needed. Use the delete option to remove any headers that aren’t required.
- Enable the Apply these request headers to the Refresh Token call toggle to include the configured headers in Refresh Token requests, if required by the external system.
Certificate-based Client Authentication
Enable the Client Certificate Exchange toggle to enforce certificate-based client authentication during the TLS handshake using a digital certificate.Testing the Authorization
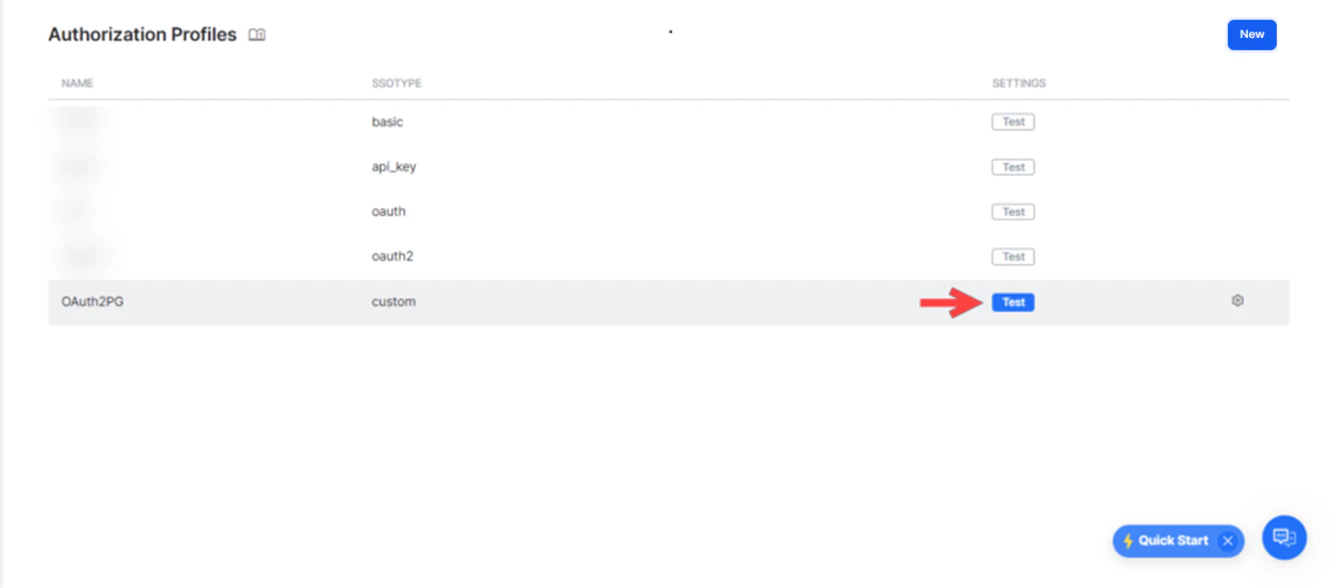
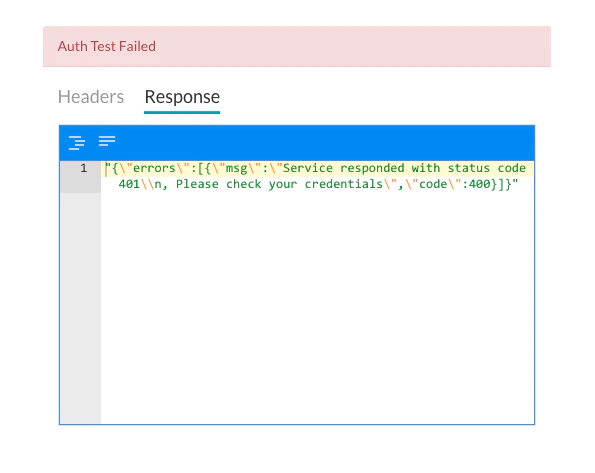
After saving the authorization, test your authorization definition by clicking Test from the Authorization Profile page.