Back to Search AI connectors list The Custom Content Connector enables Search AI to index content from applications that do not have a pre-built connector. It acts as a middleware between Search AI and a third-party application, retrieving content via REST APIs and converting it into an indexable format. A reference implementation of the connector service is available for download and serves as a template for integration. The current implementation supports basic authentication.Documentation Index
Fetch the complete documentation index at: https://koreai.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
Setup
1. Download the Service
Obtain the skeleton custom connector service from the SearchAssist Toolkit on GitHub.2. Configure the Service
- Modify
config.jsonto include the application configuration details and content fields. - Set the authorization password in the
.envfile in the root folder. Rename the existing.env.samplefile to.envand add your auth value to theAuthorizationkey.
3. Implement Changes (if needed)
Modify the service implementation as required. Refer to the readme file for details.4. Host the Service
Host the configured service on your preferred platform.Configure the Custom Connector in Search AI
- Go to Content > Connectors and select Custom Connector.
-
Configure the following fields:
Field Description Name Unique name for the connector Endpoint URL and HTTP method of the hosted service. For the default implementation: GET https://<serverip>/getContentHeaders Key-value pairs sent as request headers -
Under Headers, add the authorization header required by the default service implementation:
- Key:
Authorization - Value:
<Your-Auth-Key>(the value set in the service’s.envfile)
The encoding format for a header can be set tobase64(value is encoded before sending) ornone(value is sent as plain text). The default for newly added headers isbase64. - Key:
- Click Connect to complete the setup.
Content Synchronization
- Go to the Configurations tab of the custom connector configuration page.
- Click Sync Now.
Access Control
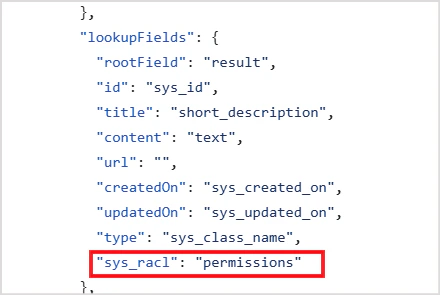
Search AI supports RACL on content ingested via the custom connector. Thesys_racl field in the connector service config.json specifies which field in your source data holds permission information. The data fetched from that field is saved as a permission entity.
For example, if access information is stored in a permissions field in your content, set the sys_racl field in the connector service config accordingly: