Back to Admin Console Bring Your Own Key (BYOK) lets your enterprise retain control of encryption keys while protecting data on the Platform. Kore.ai integrates with Azure Key Vault to use your Customer Master Keys (CMKs) for encrypting application and bot data.Documentation Index
Fetch the complete documentation index at: https://koreai.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
- Active Kore.ai subscription with BYOK enabled
- Azure account with administrative access to the Key Vault service
- Permissions to create Key Vaults
Integration Process
Step 1: Authorize the Kore Application in Your Tenant
Option 1: Admin Consent URL- Log in to the Azure portal as a Global Administrator.
- Navigate to:
- Review permissions and grant admin consent.
- Open Azure Cloud Shell or install Azure CLI locally.
- Login:
az login - Create service principal:
az ad sp create --id '<KORE-CLIENT-ID>'
Step 2: Prepare Key Vault and Key
Create a Key Vault (if one doesn’t exist):- In the Azure Portal, create a Key Vault.
- Configure:
- Resource group (select or create)
- Key vault name (unique)
- Region
- Pricing tier: Standard or Premium
- Note the Key Vault URI:
https://<vault-name>.vault.azure.net/
- In your Key Vault, go to Keys and select Generate/Import.
- Configure:
- Options: Generate
- Name: descriptive name
- Key type: RSA
- RSA key size: 2048 or 4096
- Note the Key Identifier URL.
Step 3: Configure Key Vault Access
- In your Key Vault, go to Access control (IAM) and select Add role assignment.
- Configure:
- Role: Key Vault Crypto User
- Assign access to: User, group, or service principal
- Members: Search for the Kore application name
- Select Review + assign.
Step 4: Share Information with Kore.ai
Contact Support and provide:- Tenant ID (from Microsoft Entra ID > Properties in the Azure portal)
- Key Vault URI
- Key Name
Step 5: Configure Network Access
- Recommended: Enable a private endpoint for access to the platform.
- Alternatively, allow trusted Microsoft services and Kore IP ranges.
Configure BYOK in AI for Service
After Kore.ai confirms the integration, enable BYOK in the Admin Console.- Go to Admin Console > Enterprise Key.
-
Under Bring Your Own Key, select Create Key.
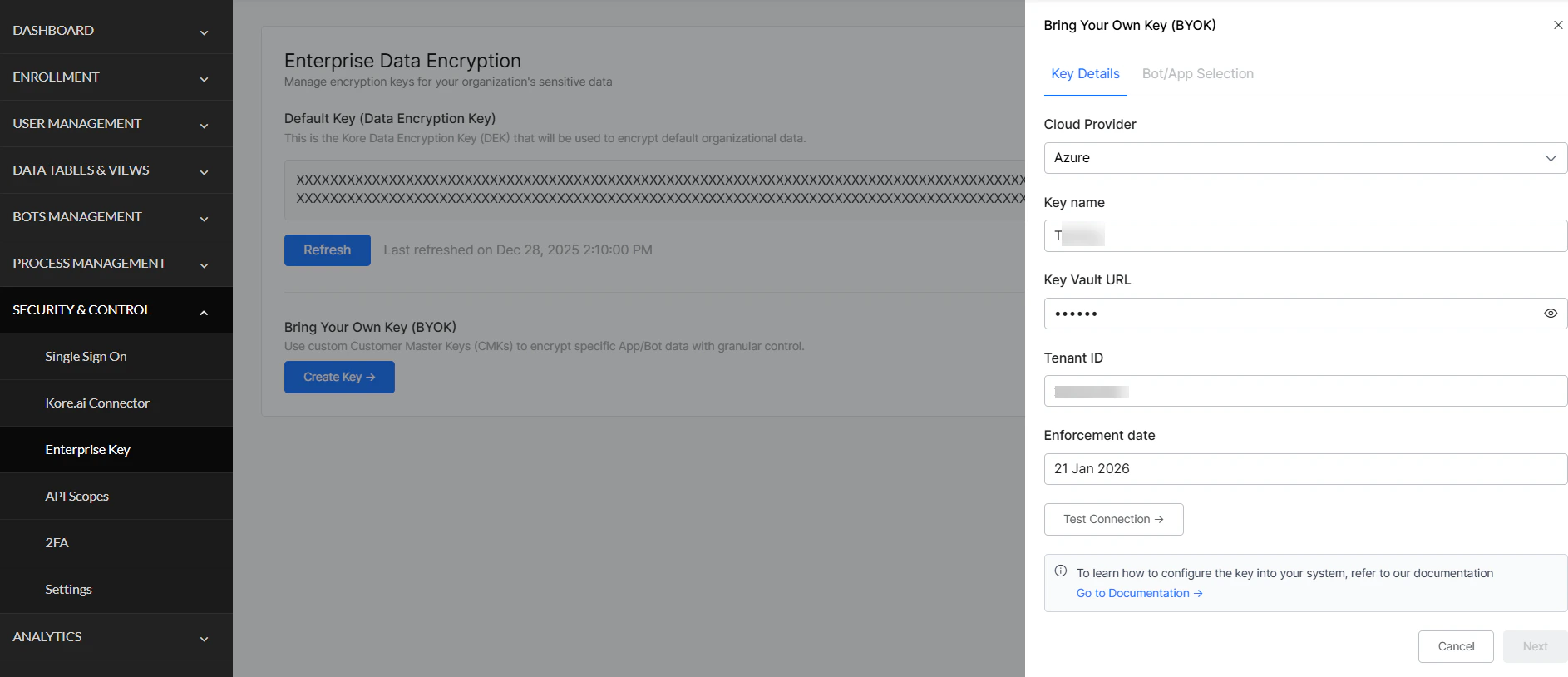
-
Enter Azure details:
Field Value Cloud Provider Azure Key identifier Your Key Vault URL Authentication credentials Your Tenant ID -
Set the Enforcement Date — the date your CMK begins encrypting data.
You can modify the CMK and retest until the enforcement date. After this date, you can only rotate the key or update which apps/bots are encrypted.
- Select Test Configuration to validate the connection (tests connectivity, authentication, encryption, and decryption).
-
Select Next to view all apps and bots.
- All apps and bots are selected by default.
- Deselect any that should remain on Kore.ai’s default encryption.
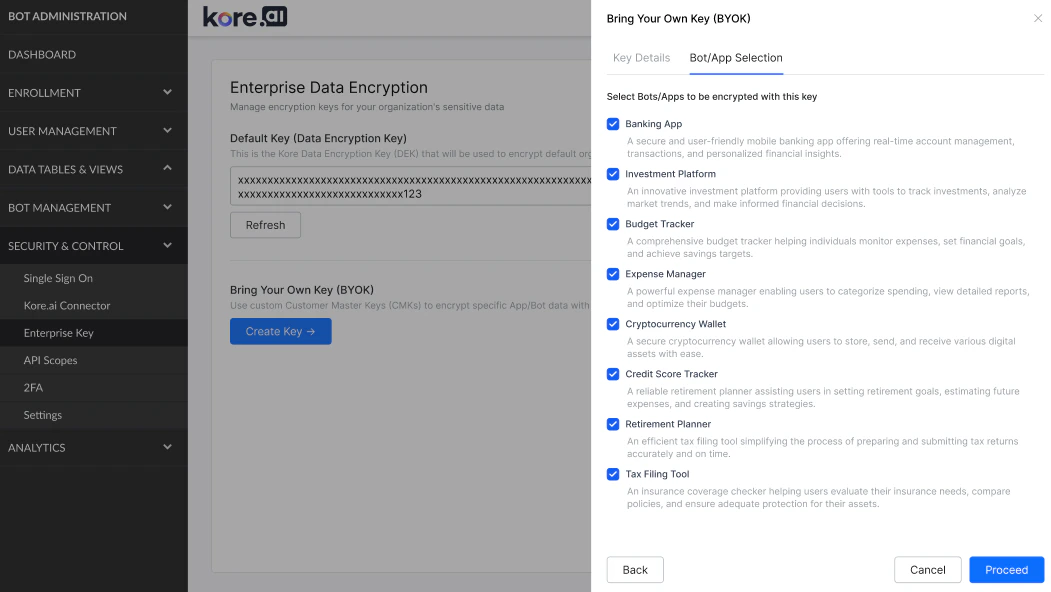
- Select Proceed to complete setup. Encryption begins on the enforcement date.
Validation (Optional)
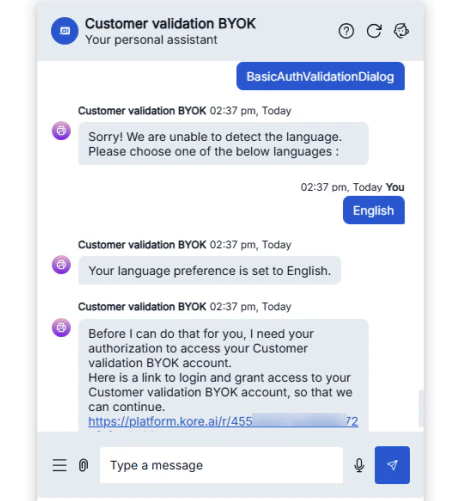
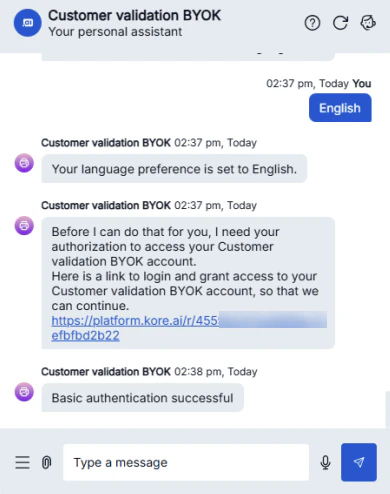
After the enforcement date, verify encryption is working. Option 1: View Analytics Check analytics data for recent chat interactions to confirm encrypted data is accessible. Option 2: Test Application Authorization- Open the application and run Authorization Profiles and Dialogs.
- Execute BasicAuthValidationDialog.
-
When the bot shows the authorization link, select it and enter credentials (
admin/password).