Back to Voice Channels Voice Gateway is a comprehensive voice automation solution that manages inbound call automation for Contact Center AI. It integrates with existing voice systems or uses the native voice processing capabilities, enabling seamless transitions between automated and human interactions within the Platform. This section covers the fundamental steps required to set up and configure your Voice Gateway for basic operation. Go to The Product (For example, Automation AI/ Contact Center AI) > Flows & Channels > Channels > Voice Gateway.Documentation Index
Fetch the complete documentation index at: https://koreai.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
Configuration
Buy New Phone Number
Steps to buy a new phone number:-
Select the Phone Numbers tab and then select Buy New Phone Number. You can configure a custom local or toll-free number by selecting Get New Phone Number on the Phone Number window.
- Select a country in the Country Name field.
- Select either the Local or Toll-Free Number option.
- Select the State.
- Enter the Area Code.
- After configuring the fields, Contact Center AI displays the monthly fee and the operational charge per minute.
-
Configure an available number with the following steps:
- Select Get Number.
- On the Forward to Phone Number page, select whether the number is reserved for Inbound Calls, Outbound Calls, or both.
- Select an App for outbound calls from the dropdown. AgentAI triggers this app when the agent makes an outbound call with this phone number.
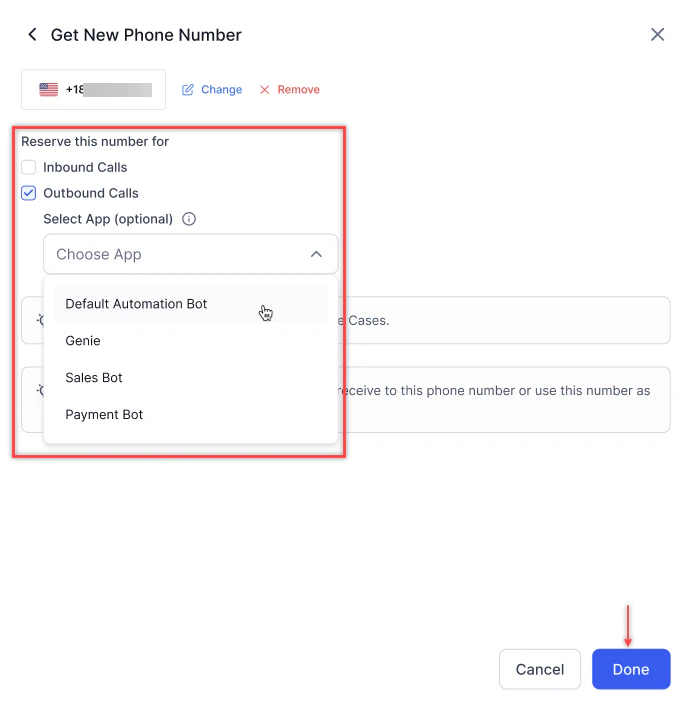
- Select Done. A success confirmation message appears.
- You can now call this number to test your Use Cases.
- When ready to go live, forward the calls you receive to this phone number or use this number as your customer support number.
This feature is only available when using our Twilio account. It’s not supported for SIP trunk setups.
Purchasing toll-free numbers
Voice Gateway doesn’t support direct toll-free number purchases due to regional regulations and documentation requirements. All toll-free numbers require manual verification and regulatory approval. To purchase a toll-free number:- Contact support and specify the required country or region.
- Support guides you through the required documentation requirements and completes procurement through Twilio.
- Configure the SIP trunk after purchase.
- The number appears in the SIP DID numbers list-Create Start Flows and associate them with the toll-free number.
Lead times vary by country and depend on local regulatory approval timelines.
Attach Flow
Steps to attach a flow to the phone number:- Select + Attach Flow. Hovering over the pie icon displays No Flow Attached.
- Select a Start Flow you want to add to this number and select Done. You can add a start flow by clicking + New Start Flow. Learn more.
- The attached flow appears. Hovering over the pie icon displays Configured.
Edit a Phone Number
Steps to edit a previously added phone number:- Select ︙ and then select Update.
- On the Forward to Phone Number page, select Change.
- Make the necessary edits, and select Done. A success confirmation message appears.
Delete a Phone Number
Deleting a phone number means stopping all services associated with it. If you remove a phone number and want to add it back later, you may be unable to do so if another user has selected it. Steps to delete an existing phone number:- Select the ︙, and select Delete.
- Select Delete to confirm your choice.
-
Alternatively, select Update, go to the Forward to Phone Number window, and select Remove. A success confirmation message appears.
The phone number cannot be deleted if there are active voice campaigns or flows attached to the channel.
SIP Trunk Setup
This option is useful when transferring calls to Contact Center AI from a toll-free or local phone number using Session Initiation Protocol (SIP) in the IVR system. Under the SIP Trunk tab, you can configure the network IPs and domains, DID number, SIP transport protocol, SIP credentials (optional), and Inbound/Outbound direction for phone numbers while the SIP URI is pre-configured. Agent AI supports real-time audio streaming through two primary methods:- SIPREC (SIP Recording): Agent AI acts as a SIPREC server, receiving duplicated audio streams from the contact center platform or a Session Border Controller (SBC).
- WebSocket Audio Streaming: For cloud-native platforms like Genesys AudioHook, Agent AI subscribes to real-time audio feeds over secure WebSocket connections.
Steps to configure SIP Trunk
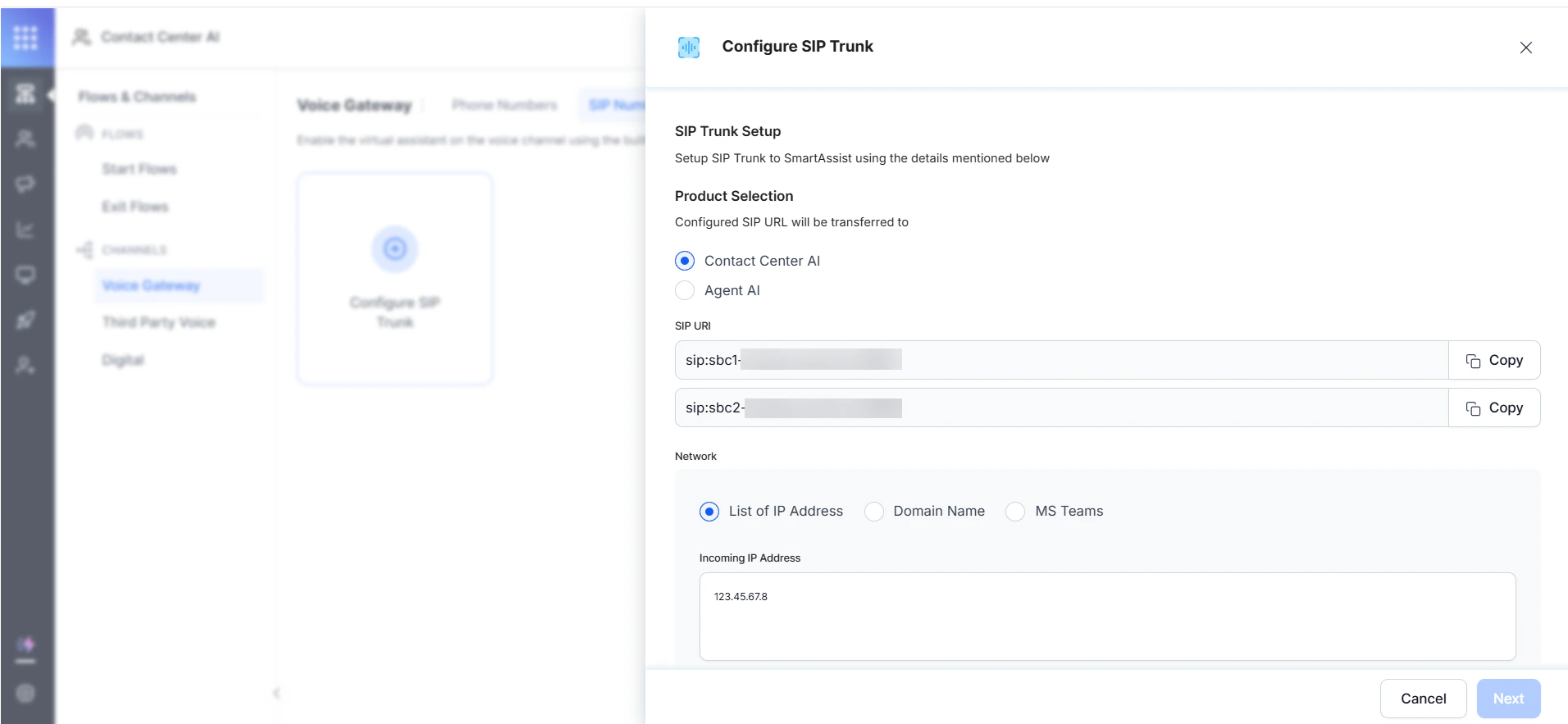
- Select Configure SIP Trunk.
-
On the Configure SIP Trunk page, configure the following:
-
Product Selection: Select the product for SIP Trunk configuration. You can select from the following options:
If you select Contact Center AI:
- SIP URI: This is a pre-configured field. A copy option enables you to copy the SIP URIs.
-
Network: To configure the Network, you can select one of the following:
-
Under List of IP Address, type the values for Incoming IP Address in the textbox.
-
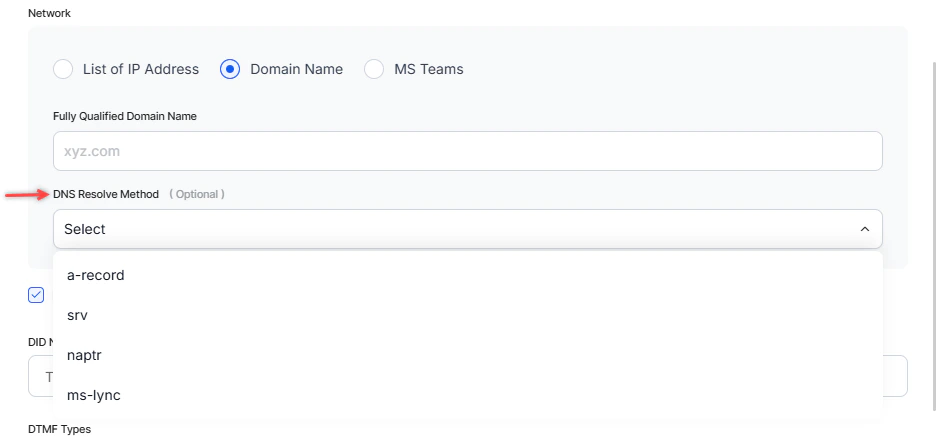
Under Domain Name, provide the following:
- Fully Qualified Domain Name (FQDN): The domain name specifies all domain levels, including the top-level domain and the root zone. Learn more.
- DNS (Domain Name System) Resolve Method (Optional): Select an option from the list to translate IP addresses to domain names for resolution when the hostname associates with multiple IP addresses. You can choose a-record, srv, naptr, or ms-lync.
-
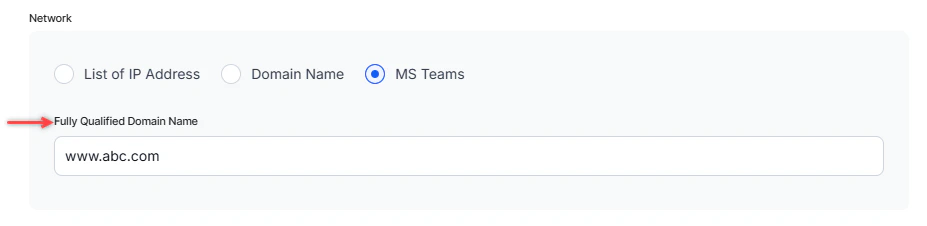
Under MS Teams, provide a Fully Qualified Domain Name (the domain name that specifies all domain levels, including the top-level domain and the root zone).
-
Under List of IP Address, type the values for Incoming IP Address in the textbox.
- (Optional) By default, the system selects E.164 Syntax. Selecting this option prepends a + before the DID number.
-
Under Direct Inward Dialing (DID) number, you can enable virtual phone numbers (SIP trunk numbers) that route calls to your existing telephone lines. You can configure SIP trunks by entering DID numbers using wildcard patterns (for example,
123*) to automatically handle multiple similar DIDs without listing each one individually. On configuring two wildcard patterns for different experience flows within an application, and a caller dials a number that matches both patterns, the system triggers the experience flow associated with the pattern that matches the most digits. Example: Map the DID numbers7896*and789654*to Experience Flow 1 and Experience Flow 2, and dial78965478, the system triggers Experience Flow 2, as789654*matches more digits than7896*.When configuring a SIP Trunk with a duplicate DID, the system behavior depends on the account and app context. For the same DID with a different IP/FQDN in the same account and app, the system prompts the user to update the existing trunk or proceed with a mandatory label. For identical DID and IP/FQDN combinations within the same account, the system blocks the configuration with an error message. DTMF (Dual-Tone Multi-Frequency) Type: (Optional) Select the DTMF type. RC2833 is the default selection. Select an option from the list for SIP Transport Type. This field sets a protocol to route SIP traffic to servers and other endpoints. The available options are TCP, UDF, and TLS. (Optional) Set the SIP Credentials (username and password) to access your SIP trunk setup account. Under SIP Termination URI, enter the IP Address/Domain Name. Configure the termination URL on your SIP trunk to enable outbound calls. - Option Ping: When selected, the system verifies access to the IP addresses. The system selects this option by default.
-
Enter the SIP Headers. You can include all available agent data in the SIP headers, enabling customers to use only the parameters relevant to their needs. The system lists the parameters as key-value pairs:
- X-AgentName:
{{agentName}} - X-AgentPhoneNumber:
{{agentPhoneNumber}} - X-AgentEmailID:
{{agentEmailId}} - X-AgentGroup:
{{agentGroup}} - X-AgentCustomID:
{{agentCustomId}} - X-AgentNickName:
{{agentNickName}} - X-QueueName:
{{agentQueue}} - X-AgentFirstName:
{{agentFirstName}} - X-AgentLastName:
{{agentLastName}}
The caller number specified in the Script Task is passed through the SIP headers when a third-party desktop application transfers the call to an agent. - X-AgentName:
-
If you select SIPREC:
- SIP URI: This is a pre-configured field. A copy option lets you to copy the SIP URIs.
-
Network: To configure the Network, you can select one of the following:
- Under List of IP Address, type the values for Incoming IP Address in the textbox.
-
Under Domain Name, provide the following:
- Fully Qualified Domain Name (FQDN): The domain name specifies all domain levels, including the top-level domain and the root zone. Learn more.
- DNS Resolve Method (Optional): Select an option from the list to translate IP addresses to domain names for resolution when the hostname associates with multiple IP addresses. You can choose a-record, srv, naptr, or ms-lync.
- Agent AI Initiated transcription: Enable or disable auto transcription. When disabled, transcription starts automatically when the SBC receives an RTP stream.
- Record the calls: Enable or disable call recordings for third-party Agent Desktop integrations. Access these recorded calls using a public API.
- (Optional) By default, the system selects E.164 Syntax. Selecting this option prepends a + before the DID number.
- Siprec Identifier: Enter Siprec identifier values.
- DTMF Type: (Optional) Select the DTMF type. RC2833 is the default selection.
- Select an option from the list for SIP Transport Type. This field sets a protocol to route SIP traffic to servers and other endpoints. The available options are TCP, UDF, and TLS.
- (Optional) Set the SIP Credentials (username and password) to access your SIP trunk setup account.
- Under SIP Termination URI, enter the IP Address/Domain Name.
- Call control parameters: Define the parameters to control the call behavior. Select Add Parameter, enter the Parameter Name and Value, and select Save. Learn more.
-
Enter the SIP Headers. You can include all available agent data in the SIP headers, enabling customers to use only the parameters relevant to their needs. The system lists the parameters as key-value pairs:
- X-AgentName:
{{agentName}} - X-AgentPhoneNumber:
{{agentPhoneNumber}} - X-AgentEmailID:
{{agentEmailId}} - X-AgentGroup:
{{agentGroup}} - X-AgentCustomID:
{{agentCustomId}} - X-AgentNickName:
{{agentNickName}} - X-QueueName:
{{agentQueue}} - X-AgentFirstName:
{{agentFirstName}} - X-AgentLastName:
{{agentLastName}}
- X-AgentName:
-
If you select WebSocket:
- Connection URL (Generate URL): Copy the auto generated URL and paste it into your third-party desktop configuration settings.
- Agent AI Initiated transcription: Turn on or turn off auto transcription. When turned off, transcription starts automatically when the SBC receives an RTP (Real-time Transport Protocol) stream.
- Record the calls: Enable or disable call recordings for third-party Agent Desktop integrations. Access these recorded calls can using a public API.
- Call control parameters: Define the parameters to control the call behavior. Select Add Parameter, enter the Parameter Name and Value, and select Save. Learn more.
-
Product Selection: Select the product for SIP Trunk configuration. You can select from the following options:
If you select Contact Center AI:
- Select Next.
- On the Forward to Phone Number window, reserve the phone numbers for Inbound Calls, Outbound Calls, or both by selecting the appropriate options.
- Select Save. Wait for up to 10 minutes after saving for the IPs to be whitelisted.
- The selected information appears on the SIP Numbers tab.
Attach a Flow
Steps to attach a flow to the SIP Number:- Select + Attach Flow. Hovering over the link icon displays No Flow Attached.
- Select a Start Flow to add to individual numbers and select Done. You can add a start flow by selecting + New Start Flow. Learn more.
- The attached flows appear. A pie icon appears under the attached flows. Hovering over the pie icon displays Configured.
You cannot attach channels to the Default Welcome Voice flow or Default Welcome Chat flow. Channels already attached to these flows continue to function as configured. However, if a channel is reattached to a different flow, it cannot be reattached to a Default Welcome Voice flow or Default Welcome Chat flow.
Edit a SIP Number
Steps to edit a previously added SIP number:- Select ︙ and then select Update.
- Make the necessary changes on the Transfer from IVR page, and select Next.
- Make the necessary changes on the Forward to Phone Number page, and select Save. A success confirmation message appears.
Delete a SIP Number
Deleting a SIP number means stopping all services associated with it. Steps to delete a SIP number:- Select ︙ and then select Delete.
- On the pop-up, select Delete to confirm your choice.
Best Practices
Voice Calls - Failures and Fallback Handling
This document outlines the comprehensive failure handling and fallback mechanisms available for voice calls in the platform. The system provides three distinct layers of failure handling to ensure robust call management and graceful degradation in the event of issues. The failure handling mechanisms are designed to address different types of failures at various stages of the call lifecycle, from initial call establishment to ongoing conversation management and error recovery. Failure Handling Mechanisms- App-Level Settings - Answer Call on Bot Response
- Default Value:
false(disabled)
- Enabled (
true): Call is answered only when the first AI Agent response is ready. - Disabled (
false): Call is answered immediately, with AI Agent response preparation occurring after call establishment.
- SIP-Specific Error Handling: Ideal for systems requiring SIP response codes for failure detection.
- Source System Integration: Enables upstream systems to handle AI Agent unresponsiveness through standard SIP signaling.
- Quality Assurance: Ensures users only hear prepared, ready responses.
- Prevents dead air or silence during AI Agent response preparation.
- Provides clear SIP signaling for upstream system integration.
- Enables proactive failure detection before call establishment.
- Experience Flow Settings - Bot No Input Section
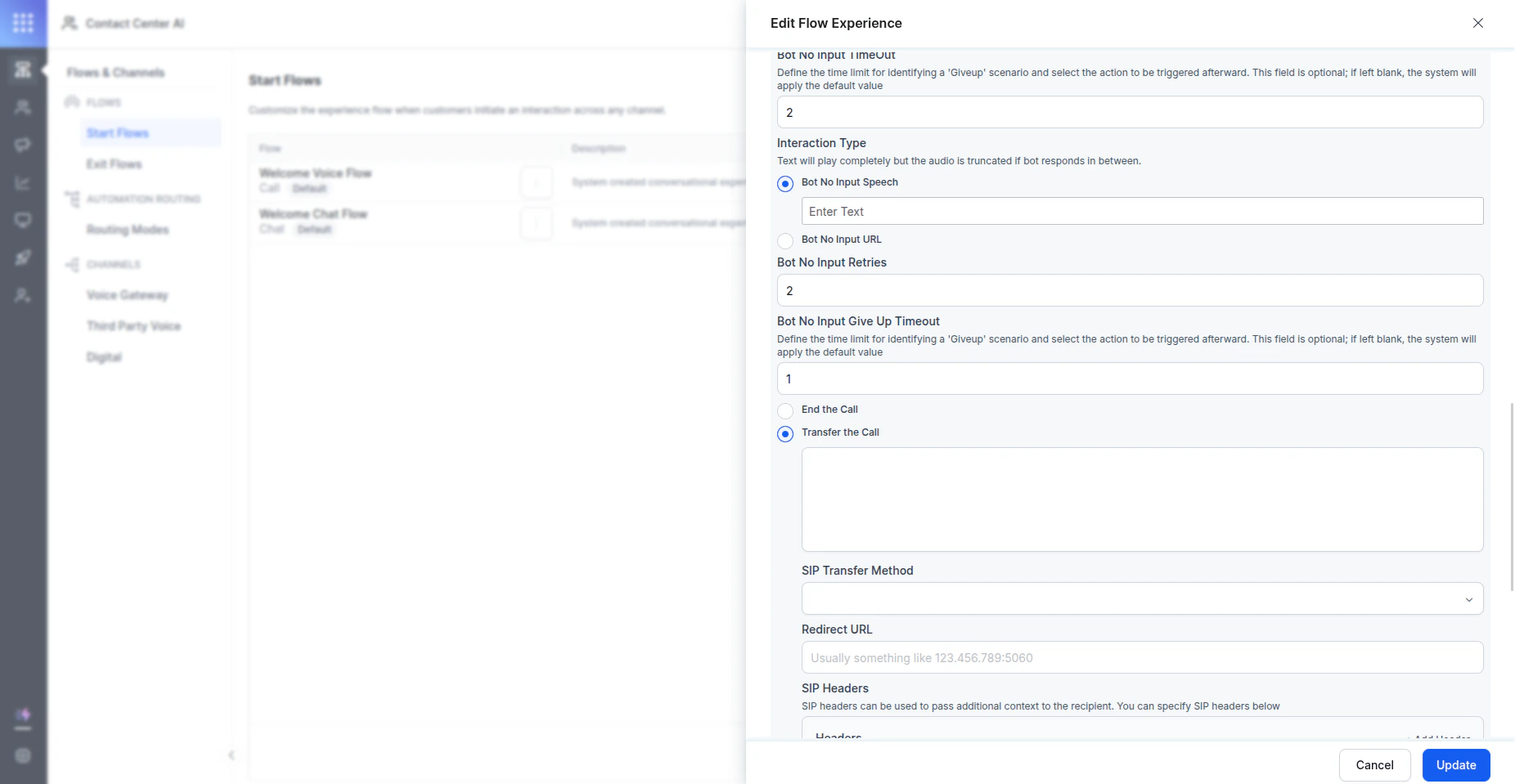
- End Call: Automatically terminates the call when the system detects the AI Agent’s unresponsiveness.
- SIP URI Target Transfer: Transfers the call to a specified SIP URI target.
- Trigger Condition: The AI Agent fails to respond within the configured timeout interval.
- Prerequisite: First AI Agent response must have been successfully delivered.
- Detection Method: Timeout-based monitoring of AI Agent responsiveness.
- Timeout Interval: Configurable duration for AI Agent response detection.
- Action Type: End call or transfer to target.
- SIP URI Target: Destination for call transfer (On selecting the transfer option).
- Automation Node Error Handling - OnError Path
- Dialog Flow Errors: Task failure events and flow execution errors.
- ASR Errors: Speech recognition failures and timeout issues.
- TTS Errors: Text-to-speech synthesis failures.
- Bot Failures: Explicit AI Agent processing errors.
- Trigger Events: System-detected errors and exceptions.
- Response Actions: Configurable error handling workflows.
- Custom Error Workflows: Define specific actions for different error types.
- Graceful Degradation: Maintain call continuity during error conditions.
- User Communication: Provide appropriate feedback to callers during error scenarios.
- Requires integration with SIP-aware source systems.
- Upstream failure detection and handling capabilities exist.
- Call quality requirements mandate prepared responses only.
- Needs SIP response codes for system integration.
- First AI Agent response delivery is successful.
- Requires ongoing AI Agent responsiveness monitoring.
- Needs fallback targets or graceful call termination.
- Prioritizes user experience continuity.
- Requires comprehensive error handling.
- Multiple error types need specific handling.
- Custom error workflows are necessary.
- System resilience is a priority.
- Always Configure: OnError path handling (universal applicability).
- Conditionally Configure: App-level settings (based on SIP integration needs).
- Scenario-Specific: Experience flow settings (based on user experience requirements).
- Always implement OnError path handling for comprehensive error coverage.
- Evaluate SIP integration requirements before enabling AI Agent-level settings.
- Define clear timeout values for AI Agent responsiveness detection.
- App-Level: Answer Call on Bot Response = true
- Experience Flow: BotNoInputGiveUp = Transfer to SIP URI
- OnError Path: Custom error handling workflow
- Call answered only when the bot response is ready.
- SIP codes are available for the upstream system handling.
- Unresponsive bot triggers transfer to fallback target.
- Explicit errors are handled through a custom workflow.
- App-Level: Answer Call on Bot Response = false
- Experience Flow: BotNoInputGiveUp = End call
- OnError Path: Standard error messaging
- Immediate call answering for a better user experience.
- AI Agent unresponsiveness results in call termination.
- Errors handled with standard user messaging.
- App-Level: Answer Call on Bot Response = true
- Experience Flow: BotNoInputGiveUp = Transfer to backup system
- OnError Path: Comprehensive error recovery workflows
- Quality-assured response delivery.
- Multiple fallback layers for different failure types.
- Maximum call continuity and user experience preservation.
ASR and TTS
Voice Preferences
This section outlines the steps to configure Automatic Speech Recognition (ASR) and Text-to-Speech (TTS) for your Voice Gateway. You can configure the voice preferences to personalize the ASR Engine and the voice that plays for your TTS conversions by going to the Voice Preferences tab and selecting Manage.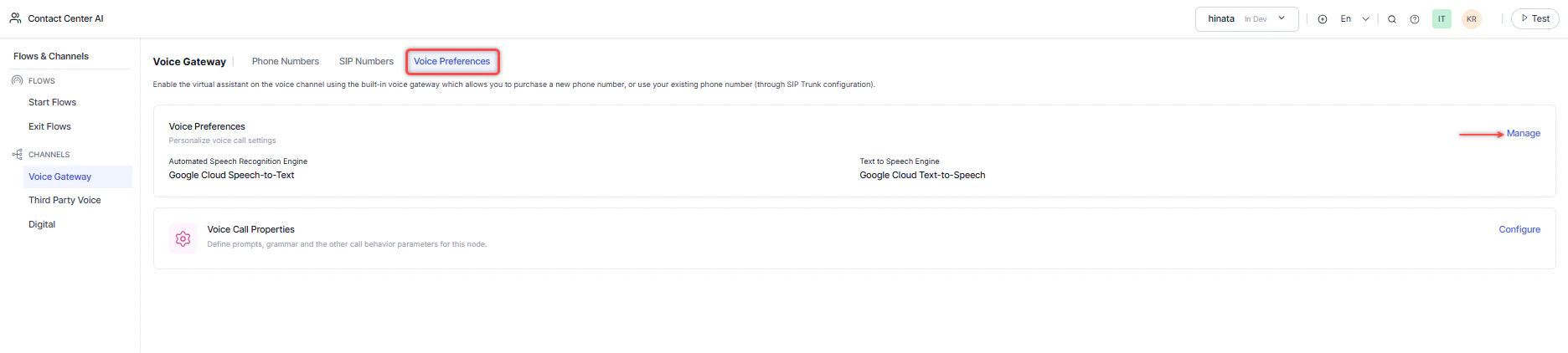
-
Select the following on the Voice Preferences window:
- Language
- Automatic Speech Recognition Engine (ASR)
-
ASR
You can choose between
- Microsoft Azure Speech Services,
- Deepgram,
- Amazon Transcribe,
- Deepgram Flux.
- Dialect
- ASR Model [BETA] (Advanced Setting)
- Primary ASR Configuration (Advanced Setting)
- Fallback ASR Configuration (Advanced Setting)
-
ASR
You can choose between
- Text to Speech Engine (TTS)
-
TTS
You can choose between
- AWS Amazon Polly,
- Microsoft Azure Speech Services,
- ElevenLabs,
- OpenAI TTS,
- Deepgram Text-to-speech.
- Voice
-
TTS
You can choose between
- Voice Preview
- Sample Text: Enter Sample Text to preview your voice selection. You can play, navigate through the audio (Back/Forward), and adjust the preview volume. Selecting the More Options (⋮) reveals options to adjust Playback Speed. Select Play next to any available voice to preview it. Voices are available for all TTS engines, but each engine has its voice options. Select a different Voice Language if required.
- TTS Model [BETA] (Advanced Setting)
- Primary TTS Configuration (Advanced Setting)
- Fallback TTS Configuration (Advanced Setting)
-
Select Done once you have completed configuring your voice preferences. The set voice, language, and dialect apply to automated customer responses that use text-to-speech.
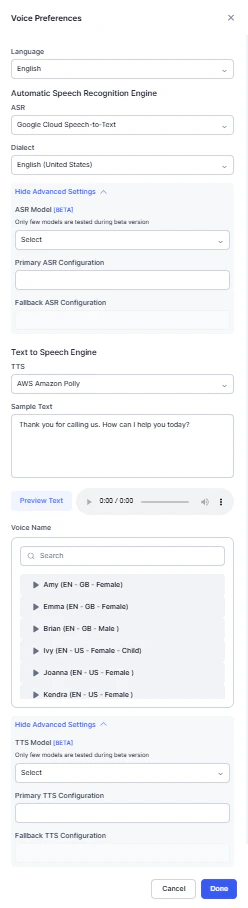
If a “TTS ERROR” appears when you dial a Voice Call and execute the Start Flow attached to an automation, the issue might occur because the voice name is not properly selected in the configuration. Even if you select a voice and save the changes, the system might not register the selection. Reselect the voice and make a small edit in the flow description (for example, add or remove a character). This action prompts the system to recognize the change and ensures that the TTS functions correctly and the audio plays as expected.
Configure ASR (Automatic Speech Recognition)
Configure Primary and Fallback ASR/TTS
ASR/TTS Fallback functionality can be implemented at various levels within the system, such as the application level, experience flow level, or even the call control parameter level. This mechanism ensures that if there is an error or failure with the primary ASR (Automatic Speech Recognition) or TTS (Text-to-Speech) service, the system automatically switches to a secondary, or fallback, ASR/TTS configuration. By doing this, the fallback prevents interruptions in the service and ensures a seamless user experience, regardless of issues with the primary configuration.- For optimal performance, it’s advised to configure the fallback with the same vendor in a different region/label.
This feature is available only in SmartAssist and not implemented in AI for Service. We will implement it in the next releases. For now, you can add Primary & Fallback ASR/TTS from the same vendor only. Example: If you have selected the Microsoft Azure Speech Services vendor as the ASR, you can enter a label name from the Microsoft vendor itself, such as
my_azure-US. You can configure the label name in Primary ASR/TTS configuration and Fallback ASR/TTS configuration under Show Advanced Settings. The fallback ASR/TTS configuration should not be the same as the Primary ASR/TTS configuration. Both Primary and Fallback ASR/TTS configurations should be available in VG Speech Services otherwise you will not be able to configure in SmartAssist. The Credential Status of the Speech services configured in VG should be verified. If credential status is failed then ASR/TTS conversations fail. In Call control parameters, - You can configure the fallback for different vendors. But for optimal performance, it’s advised to configure the fallback with the same vendor in a different region. In-call control parameters dont have any validation of duplicate values for Primary and Fallback configurations, so you have to pay closer attention to spelling mistakes.Supported ASR, TTS, and Voice Biometrics Providers
Voice Gateway supports integration with third party ASR, TTS, and Voice Biometrics providers. Learn moreSupported Languages and Dialects
The following languages and dialects are supported:| English (Australia) | English (Nigeria) |
|---|---|
| English (Canada) | English (Pakistan) |
| English (Ghana) | English (Philippines) |
| English (Hong Kong) | English (Singapore) |
| English (India) | English (South Africa) |
| English (Ireland) | English (Tanzania) |
| English (Kenya) | English (United Kingdom) |
| English (New Zealand) | English (United States) |
Use Custom ASR and TTS Credentials (BYOK)
Integrate your own Automatic Speech Recognition (ASR) and Text-to-Speech (TTS) licenses with the Voice Gateway instead of using the default providers. Follow the steps to securely configure and use your credentials.Initiation and Security
The platform manages custom provider onboarding through a controlled support process to protect sensitive API keys.- Contact support and request a Custom Provider Configuration.
-
Provide your credentials using one of the following methods:
- Send the credentials to your assigned support representative.
- Schedule a session with the technical team and share the credentials.
Provider Labeling
After Support receives your credentials, the system maps them to a unique identifier in the Voice Gateway. Label Creation: The system generates a unique label name (for example, Custom_Nuance_V2) for your account. Activation Confirmation: Support sends a confirmation email after activating the label.Implement in Call Flows
To use your custom ASR or TTS provider in a call or session, pass the assigned label in the call control parameters of your API request or dialog task.| Parameter | Description | Example Value |
|---|---|---|
sttLabel | Unique label for your custom Speech-to-Text provider | "MyAzureSTT" |
ttsLabel | Unique label for your custom Text-to-Speech provider | "MyGoogleTTS" |
Best Practices
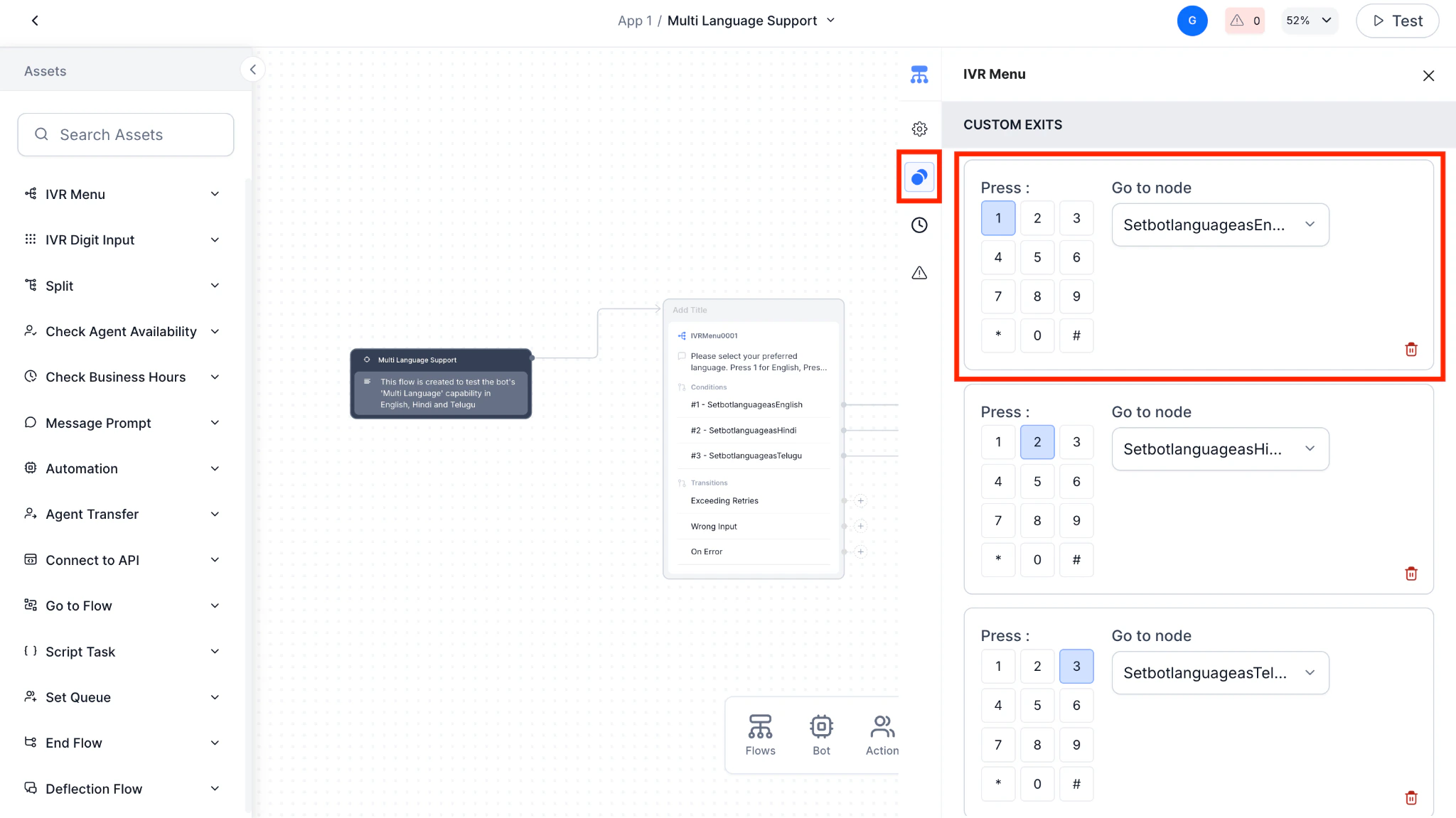
Multi-Language App Setup
This guide details the process for setting up a multilingual App that can switch languages based on the caller’s selection. We’ll cover the steps for both the Experience Flow (how the call routes) and the Dialog Flow (how the AI Agent responds). Understanding the Use Case The primary goal is to let a caller choose their preferred language (for example, by pressing a number on their phone) and have the AI Agent immediately start communicating with them in that language. This ensures a smooth, user-friendly experience from the first interaction. Steps to configure a Multilingual App: Step 1: Add Languages to Your Platform Before you can use a language in an App, you need to enable it on the platform.- Sign in to AI for Service and select the Product Switcher.
- Go to Settings > Language Management.
- Select + Add Language and select the languages your AI Agent supports, such as English, Hindi, and Telugu.
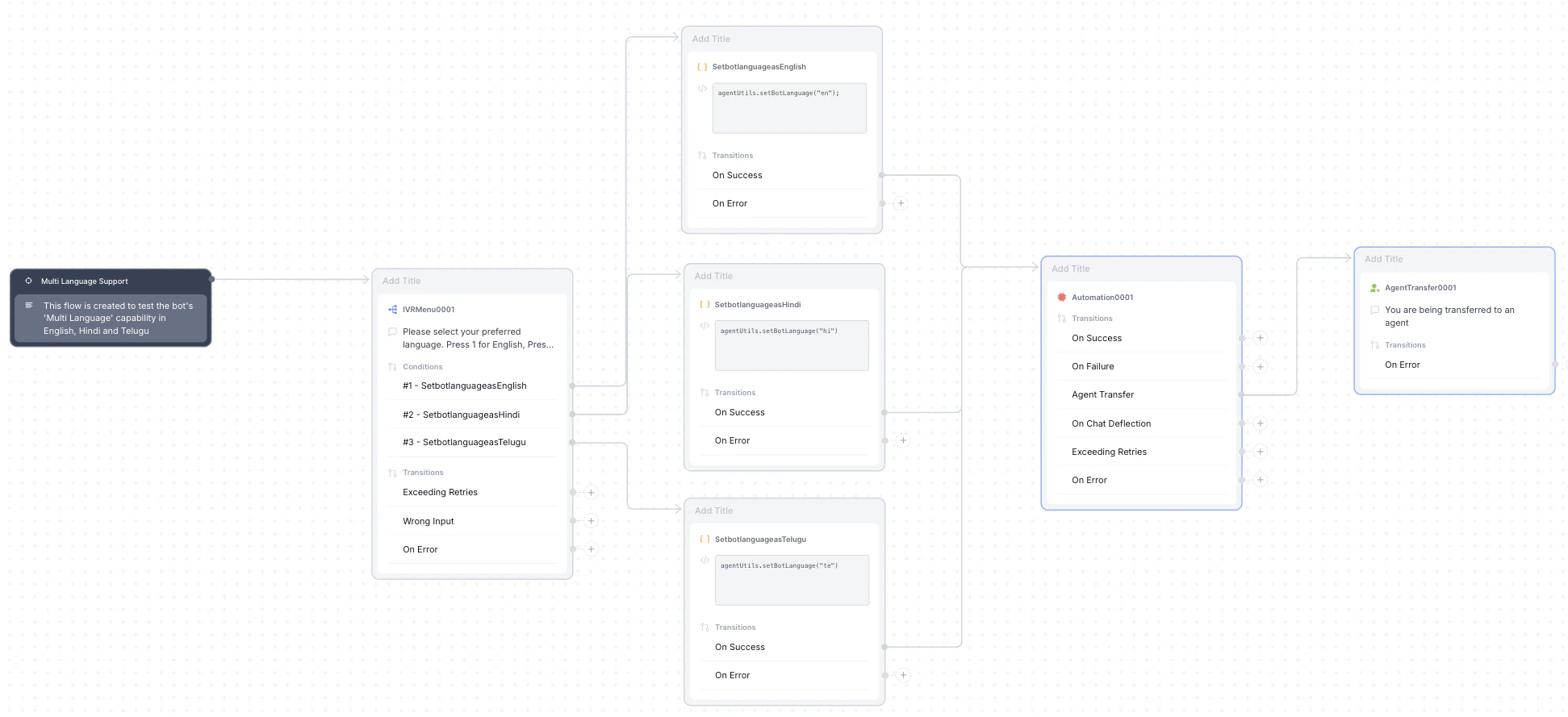
- Create a new Flow.
- After the Start node, drag an IVR Menu node.
-
In the IVR Menu node, create prompts for each language option (for example, “Press 1 for English,” “Press 2 for Hindi,” “Press 3 for Telugu”).

-
For each language option, connect the number key (for example, “1”) to a new Script node. This is the key step where the language is set.
-
For each Script node:
- Assign a name, such as ‘Set Language to English’.
-
In the ‘Define a Script’ section, add the following code, replacing
<language code>with the correct lowercase code for that language: -
JavaScript
agentUtils.setBotLanguage('<language code>');- Example for English:
agentUtils.setBotLanguage("en"); - Example for Hindi:
agentUtils.setBotLanguage("hi"); - Example for Telugu:
agentUtils.setBotLanguage("te");
- Example for English:
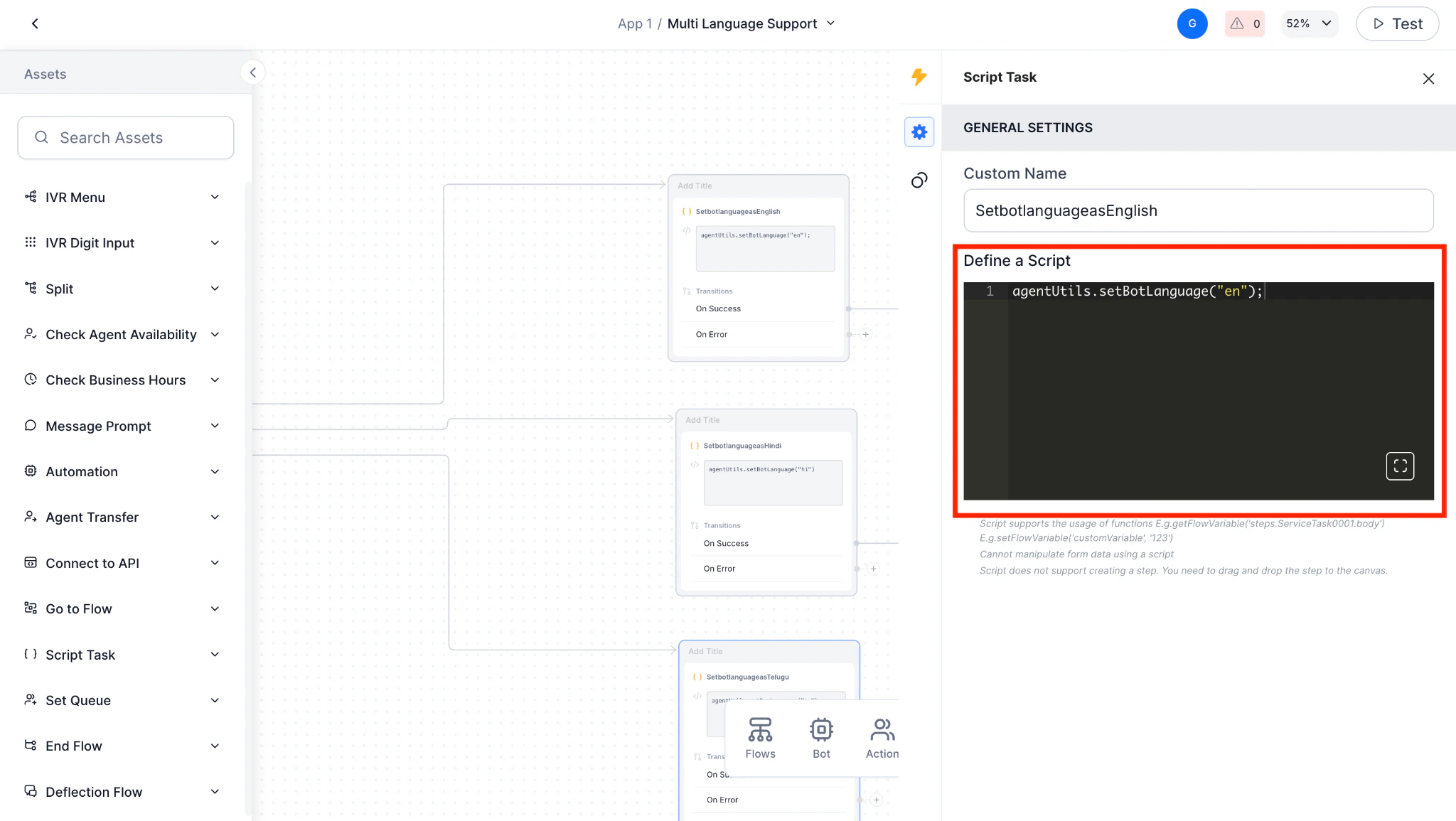
Use two-letter language codes in lowercase. For example, use “en”, not “EN”, “hi”, not “HI”,
- Connect all nodes to a Run Automation node. This triggers the main part of your AI Agent’s logic, the Dialog Flow.
-
Inside the Run Automation node:
- Under Automation AI options, select Run a specific Dialog.
-
Choose the Dialog Flow you’ve built for your AI Agent.

- Configure ‘Agent Transfer’ under ‘Connection Rules’.
-
Reference configuration of the entire flow.
- Open the Dialog Flow you connected in the previous step.
-
The platform enables you to configure different languages within the same flow. Look for a language selector on the app header.
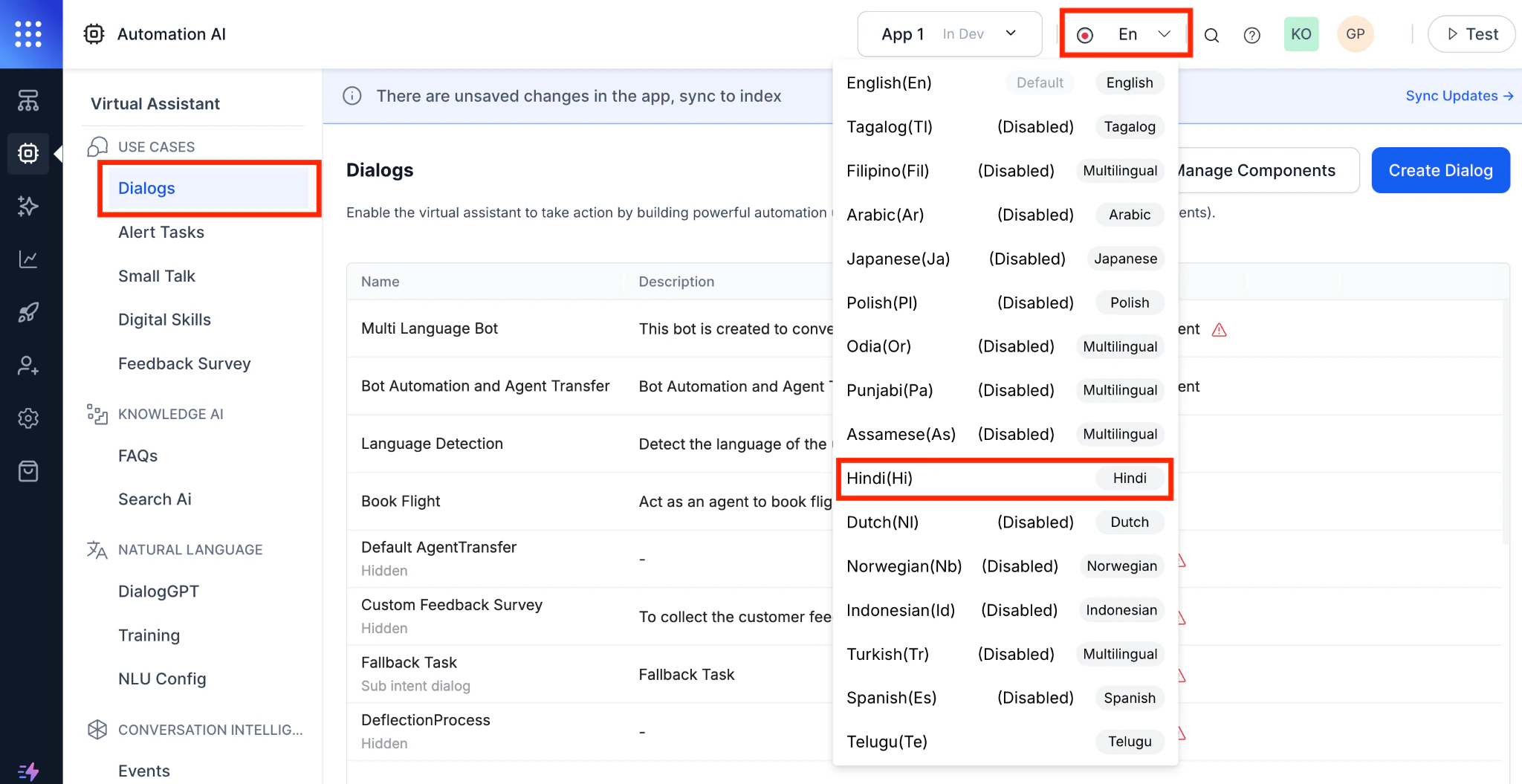
- Select a language (for example, Hindi) from the dropdown. Now, any text you add to nodes associate with this language.
-
For each node (like a Message node or Entity node), enter the text in the selected language.
Example: For a Message node, if you’ve selected Hindi, you’ll enter the Hindi text in the Bot Response box.
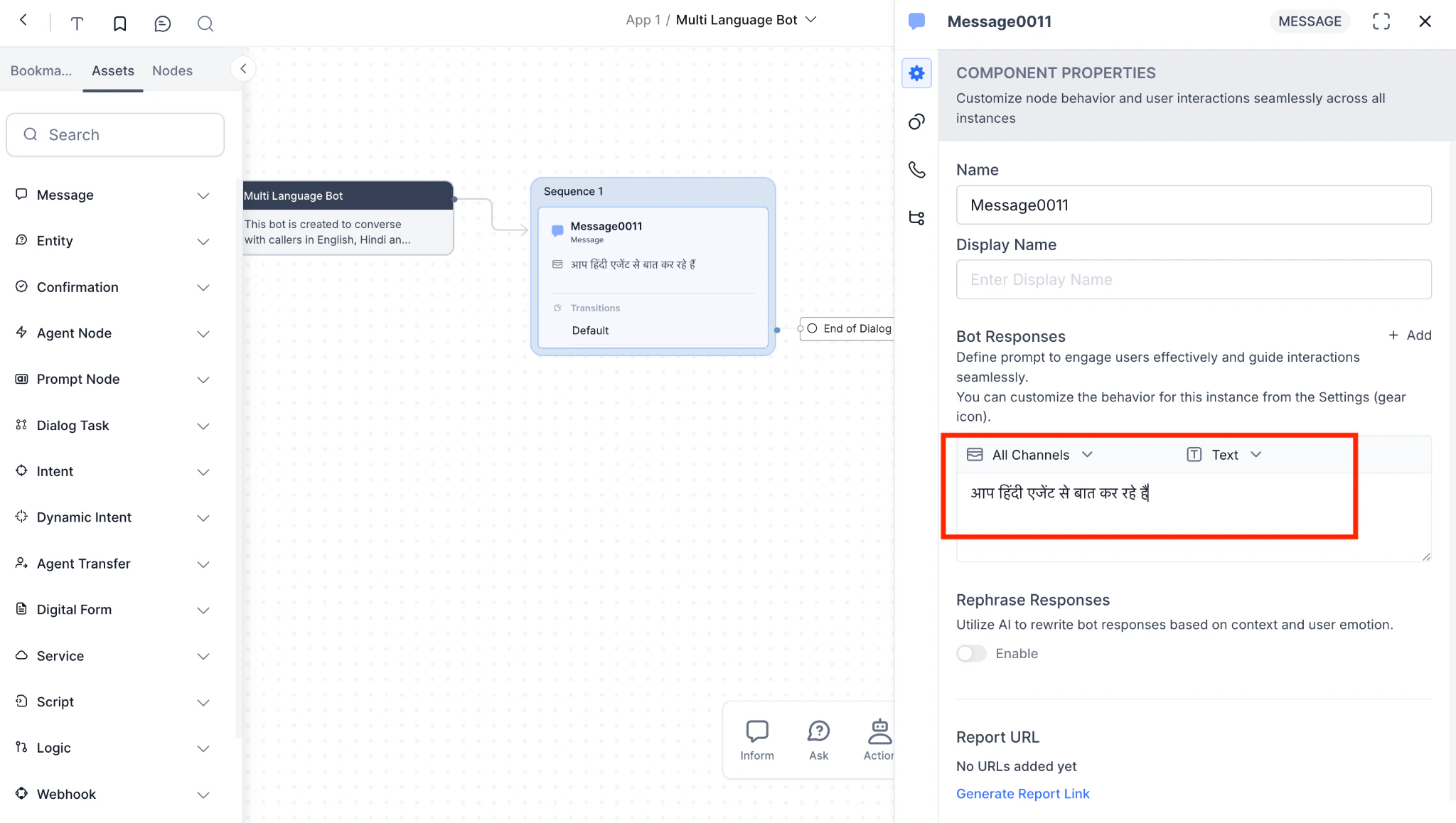
- Repeat this process for every language that the AI Agent supports. Switch the language selector and add the corresponding text for each node. This makes it easy to manage a single flow with all language variations.
- In a specific Dialog Flow node (for example, a Message or Entity node), select the IVR Properties tab.
-
You can set specific call control parameters that override the default settings. This is useful for:
-
Using a different TTS provider or voice in a particular language.
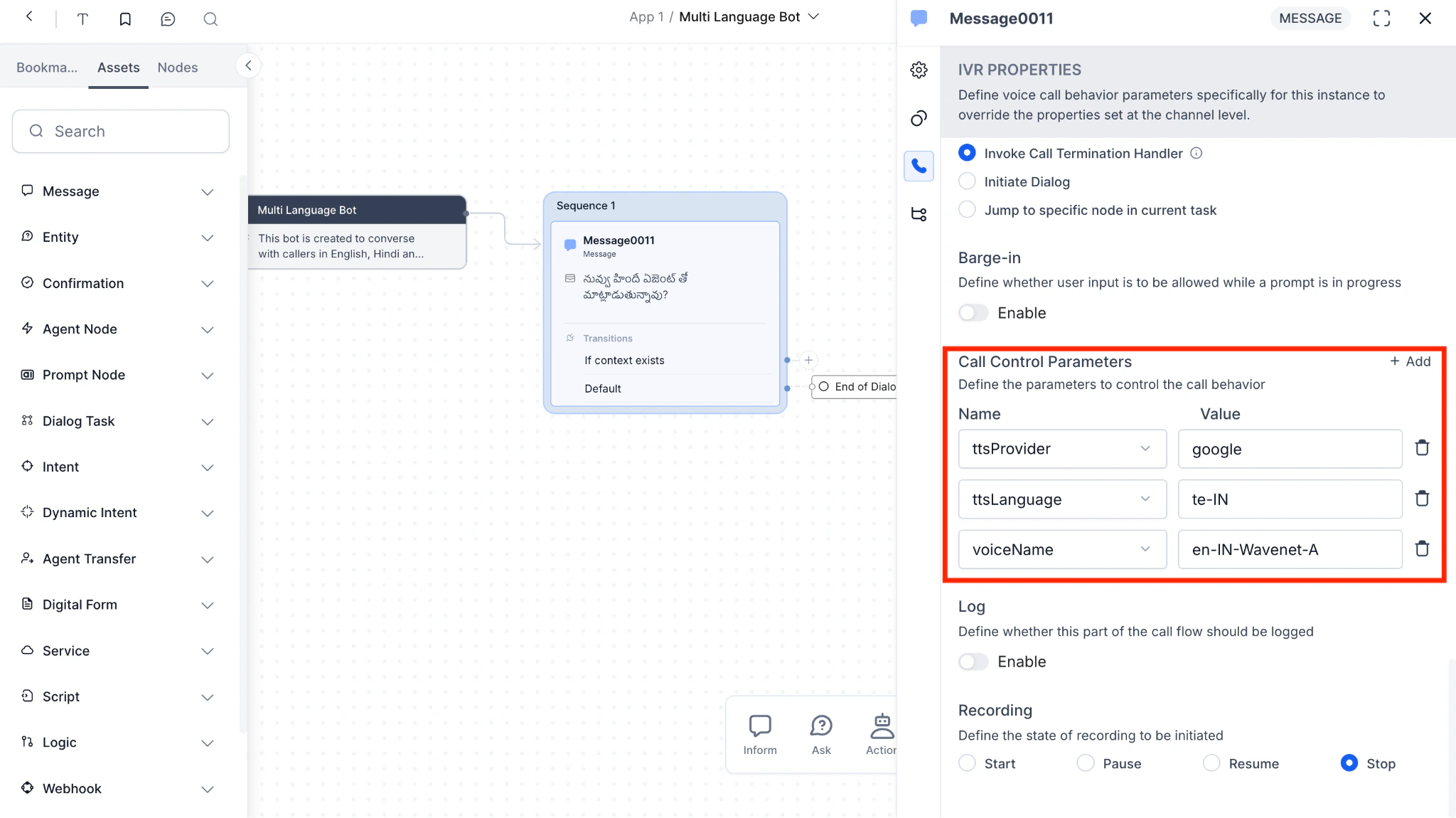
-
Choosing a different ASR provider that’s better at understanding a particular accent or language.
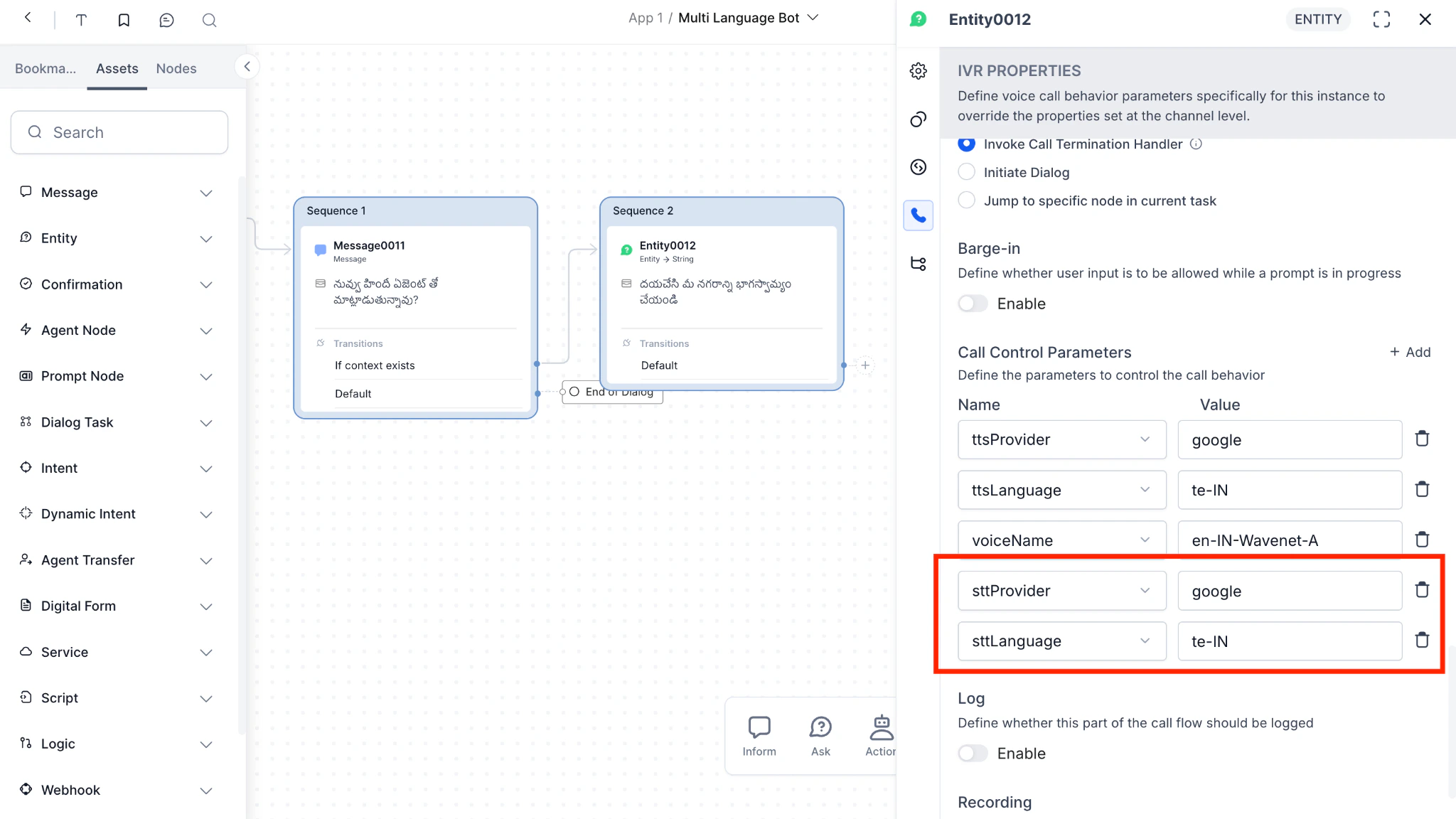
-
Using a different TTS provider or voice in a particular language.
Double-check that the language codes are in lowercase in the script node and that you’ve configured both the IVR and the Run Automation nodes correctly.
Audio Tags (ElevenLabs v3)
Setting the ElevenLabs v3 Model To use ElevenLabs v3 and its audio tags feature, you must first set themodel_id to eleven_v3 using the ttsOptions call control parameter. You can do this at two levels:
- Channel level-Applies the v3 model globally to all calls on the channel. See Channel Level Call Control.
- Node level-Applies the v3 model at a specific point in the conversation flow (for example, in a Script Node or Script Task). See Node Level Call Control.
- Go to Flows & Channels > Channels > Voice Gateway.
- Navigate to the SIP Trunk tab and select your SIP trunk configuration.
- Under Call control parameters, select Add Parameter.
-
Set the Parameter Name to
ttsOptionsand the Value to: - Select Save.
Audio tags (for example,
[excited], [whispers]) are only supported with the eleven_v3 model. Ensure the model is set before using audio tags in your prompts. For more details on ttsOptions, see Structure of ttsOption` > ElevenLabs. [excited], [whispers]). The TTS engine interprets these tags as stage directions and adjusts emotional tone, delivery style, and non-verbal cues in the generated audio.
This capability is available only with the ElevenLabs v3 (eleven_v3) model.
You can insert audio tags anywhere in a script to modify delivery in real time. Use a single tag or combine multiple tags to create complex emotional transitions within the same prompt.
Audio tag categories and examples
| Category | Example Tags | Example Usage |
|---|---|---|
| Emotions | [excited], [sad], [angry], [calm], [dramatic], [eager] | [excited] Your order has been shipped! |
| Delivery Style | [whispers], [shouts], [rushed], [slowly] | [whispers] Please stay quiet. |
| Human Reactions | [laughs], [sighs], [clears throat], [gulps] | [sighs] I'm sorry to hear that. |
| Accents | [British accent], [American accent] | [British accent] Hello, how are you? |
- Match context and voice: Audio tags work best when they align with the natural personality of the selected voice.
- Use punctuation intentionally: The V3 model interprets punctuation as delivery cues. Ellipses (
/ai-for-service/channels/voice-gateway.) introduce pauses, and capitalization increases emphasis. - Confirm model selection: Configure voice settings to use the
eleven_v3model. Audio tags don’t work with earlier models. - Ignore tag casing: Audio tags are case-insensitive.
[HAPPY]and[happy]behave the same way.
- Open the Dialog Task and select a Message Node, Entity Node, or Confirmation Node.
- Navigate to User Prompts or Bot Responses and select the Plain Text tab. If you use dynamic responses, open the JavaScript editor.
-
Add bracketed tags at the exact point where the delivery changes.
Example:
[warmly] Hello! [pause] How can I assist you today? - Save the node. Voice Gateway sends the tagged text to ElevenLabs for processing.
- Behavior: The platform sends the entire tagged prompt to ElevenLabs in a single request.
- Audio generation: The TTS engine generates the full audio output and applies emotions sequentially based on the tags.
- Recommended use: Short responses where minimal latency is acceptable.
- Feature maturity: Audio tags are an Alpha feature. Sometimes, the model may read tags aloud or ignore them if the selected voice doesn’t support the requested emotion.
- Character limit: ElevenLabs V3 supports approximately 5,000 characters per request.
- Voice compatibility: Professional Voice Clones (PVCs) aren’t completely optimized for V3. Use Instant Voice Clones (IVCs) or prebuilt voices for best results.
Voice Call Properties (Account Level)
This section describes global voice call properties that apply to your entire Voice Gateway setup. Voice call properties are fundamental aspects that define the quality and reliability of communication over Voice Gateway. These properties include End of Task Behavior, Event Configuration, Call Termination Handler, Call Control Parameters, Timeout Prompt, Barge-in, Timeout, and No. of Retries, which collectively determine the user experience during a voice call. Configuring these properties is crucial for ensuring seamless and effective voice communication over network infrastructures. You can configure the voice call properties by going to the Voice Preferences tab and selecting Configure on the Voice Call Properties section.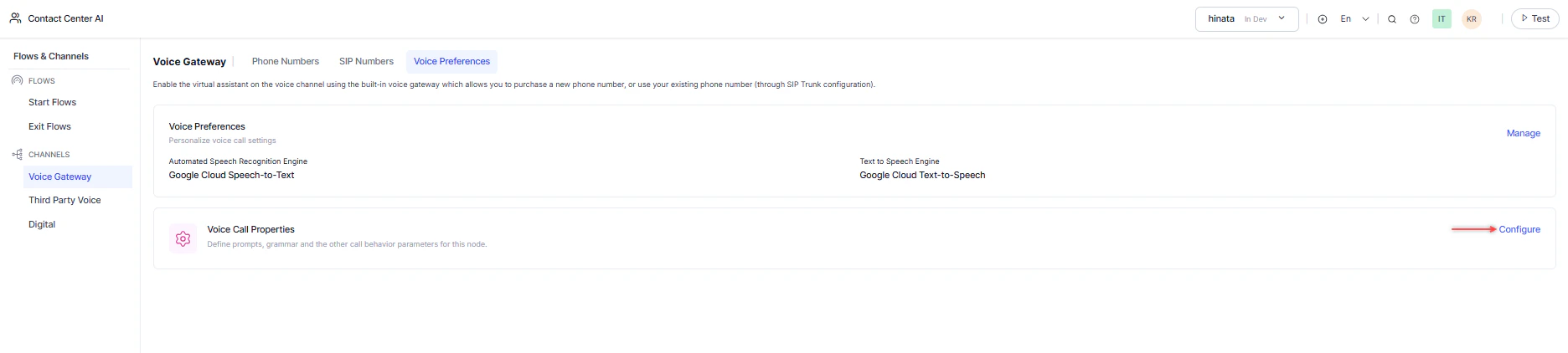
End of Task Behavior
Define the app’s behavior when reaching the end of a task. You can choose the following actions:- Trigger End of Task Event
- Terminate Call

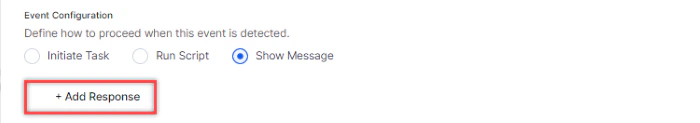
Event Configuration
Define how to proceed on detecting this event. You can choose the following actions:-
Initiate Task: Select a task from the dropdown menu that initiates on detecting the event.
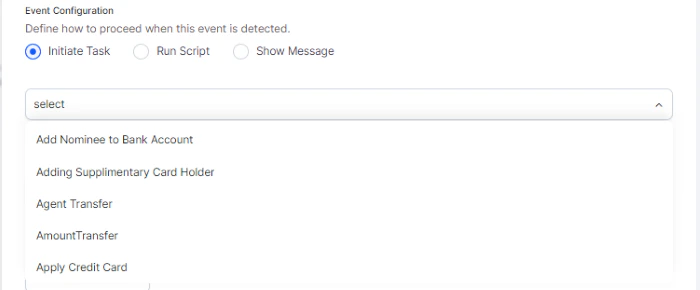
-
Run Script: Enter the script that runs on detecting the event.
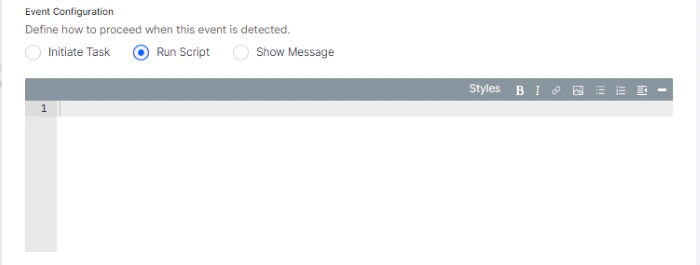
-
Show Message: Select + Add Response, enter the message that displays on detecting the event, and select Done.
Call Termination Handler
Specify the intent (dialog) to handle the call termination event from the dropdown.
Timeout Prompt
Define prompt to be played when user input isn’t received within the time-out period.Barge-in
Define whether user input is allowed while a prompt is in progress. By default, this option is un-available.Timeout
Define the maximum wait time to receive user input. The maximum wait time is 60 seconds.No. of Retries
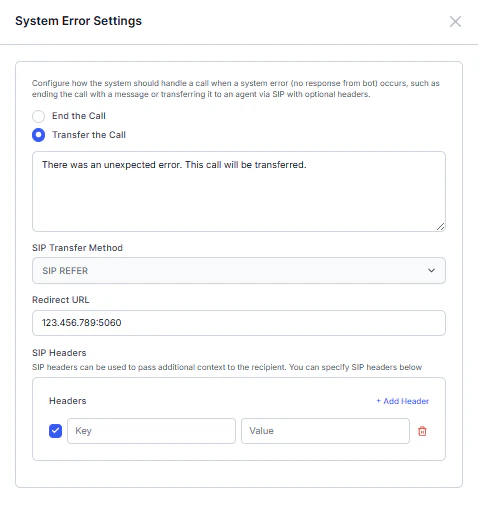
Define the maximum number of retries allowed. Select Save. A success message appears, and saves the voice call properties.System Error Settings
Configure how the system handles a call when a system error occurs (no response from the bot), such as ending the call with a message or transferring it to an agent via SIP with optional headers. End the Call- Select End the Call and enter the message to play before the call ends.
- Select Save
- Select Transfer the Call and enter the message to play before the call transfer.
- The SIP Transfer method is pre-filled.
- Enter the Redirect URL. For example,
sip:123.456.789:5060. - (Optional) Enter the SIP Headers (Key and Value). For example,
X-Reason: SystemError. - Select Save.
Configure Different “Refer-To” Numbers for Different Experience Flows
In the current bot configuration, System Error Settings apply globally across all experience flows in the bot. However, in scenarios where different Lines of Business (LOBs) use different experience flows, you can configure system errors to transfer calls to different phone numbers depending on the LOB. This can be achieved by:- Passing the Refer-To phone number through a SIP Header in the SIP INVITE request.
-
Dynamically reading that header in System Error Settings using the format:
{{SIPHEADER.<header_name>}}Example: Redirect URL:{{SIPHEADER.contact}}This dynamically determines the transfer destination based on the header value received in the SIP INVITE.
Configuration
Step 1. Configure System Error Settings Navigate to the System Error Settings configuration in your bot and enter in the following details.| Field | Value |
|---|---|
| Message | Any preferred system error message |
| SIP Transfer Method | SIP Refer (pre-filled) |
| Redirect URL | {{SIPHEADER.contact}} |
| SIP Headers | Optional–include any headers needed for context |
sip:+14085550100@example.com
Step 3. Example SIP INVITE Request
Below is a sample SIP INVITE message sent to the Voice Gateway.
| Header | Description |
|---|---|
| Contact | Contains the Refer-To number for fallback routing |
| Redirect URL | Configured in System Error Settings as {{SIPHEADER.contact}} |
- Reads the Contact header value from the SIP INVITE
- Resolves the Redirect URL dynamically
-
sends a SIP REFER to transfer the call to:
sip:+14085550100@example.com
| LOB | SIP Header Value |
|---|---|
| Banking | Contact: sip:+14085550100@example.com |
| Insurance | Contact: sip:+14085550200@example.com |
| Retail | Contact: sip:+14085550300@example.com |
sip:+14085550200@example.com
- System Error Settings are configured at the bot level and apply to all experience flows.
- Dynamic routing is enabled by passing the Refer-To number in the SIP headers of the SIP INVITE.
- The Redirect URL must use the format
{{SIPHEADER.<header_name>}}to read header values dynamically. - Ensure the correct header name used in the Redirect URL matches the header sent in the SIP INVITE.